BUU-Crypto
password
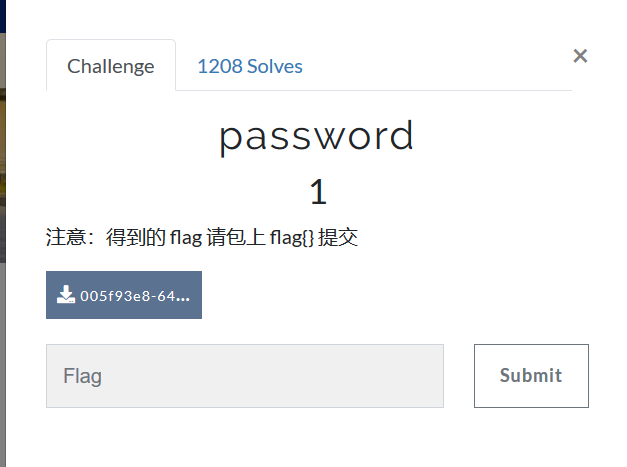
打开后得到题目:
找了一圈没有其他提示,直接把张三和生日连起来,当作flag提交,得到张三的缩写和生日连接起来是flag
即:
flag{zs19900315}变异凯撒
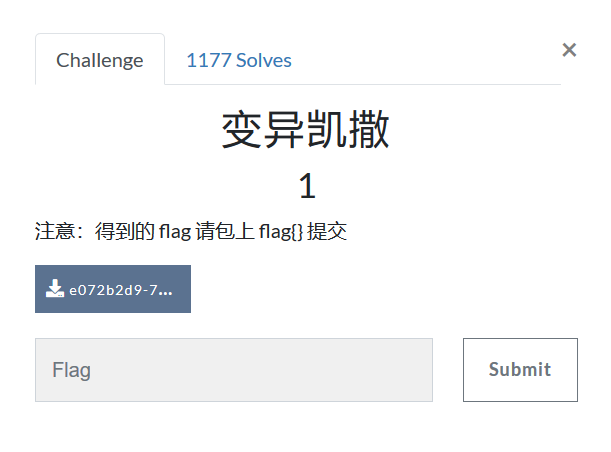
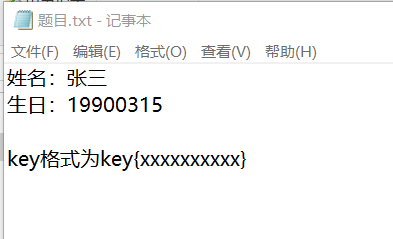
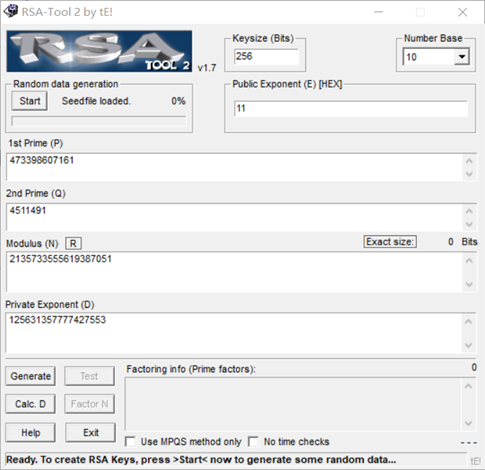
打开题目后得到密文:
afZ_r9VYfScOeO_UL^RWUc
题目已经提示了是变异凯撒,那么首先要知道凯撒加密的原理是偏移替换。所以这里可以直接根据ASCII找规律。即密文中a—97 ,f—102,Z—90,_—95 。而这四个应该对应的是flag,即102,108,97,103。由此得到偏移规律为+5,+6,+7,+8。那么根据此规律编写脚本:
得到:
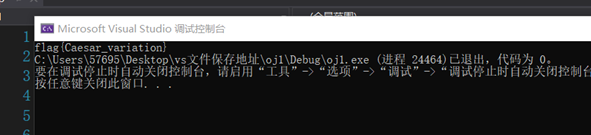
即:
flag:flag{Caesar_variation}Quoted-printable

密文:=E9=82=A3=E4=BD=A0=E4=B9=9F=E5=BE=88=E6=A3=92=E5=93=A6
包括密文也好,题目也好,都可以看出是quoted-printable编码。那么直接找到对应的在线解码工具,解码得到:
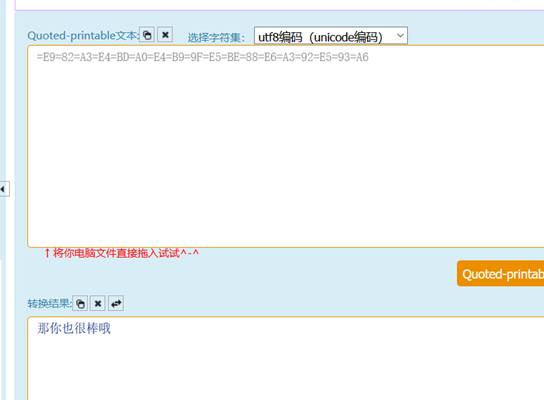
即得到:
flag{那你也很棒哦}丢失的MD5

下载后是一个py文件,打开后如下:
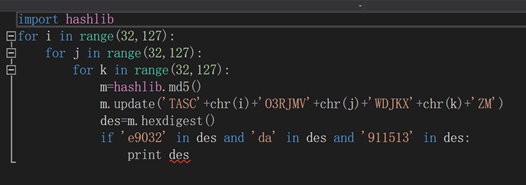
写出脚本如下:
import hashlib
for i in range(32,127):
for j in range(32,127):
for k in range(32,127):
m=hashlib.md5()
m.update('TASC'.encode('utf-8')+chr(i).encode('utf-8')+'O3RJMV'.encode('utf-8')+chr(j).encode('utf-8')+'WDJKX'.encode('utf-8')+chr(k).encode('utf-8')+'ZM'.encode('utf-8'))
des=m.hexdigest()
if 'e9032' in des and 'da' in des and '911513' in des:
print (des)得到:
即:
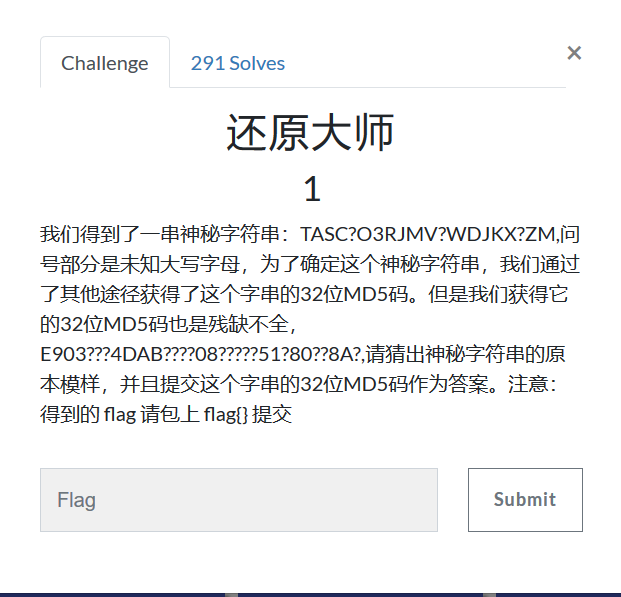
flag{e9032994dabac08080091151380478a2}大帝的密码武器

下载后将文件改为zip格式,然后得到密文和提示
密文:
提示:
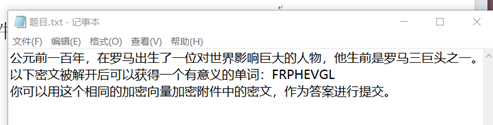
即,把该单词进行位替换,找到有意义的单词。结果如下:

那么只需要把密文以13向量位移加密:

即得到flag:
flag{PbzrPuvan}传统知识+古典密码
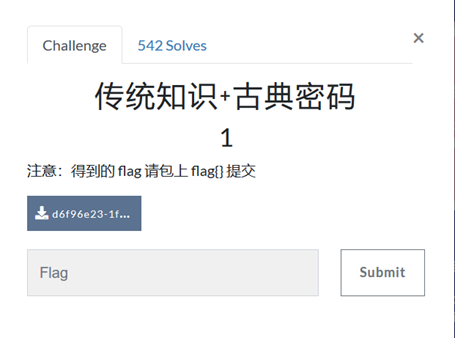
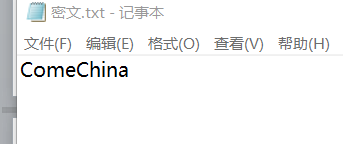
下载得到密文:
由于范围是传统知识,那么对应的只有两种可能,一是顺序,二是年份。而其中顺序得不到有用数据,那么就是年份
辛卯,癸巳,丙戌,辛未,庚辰,癸酉,己卯,癸巳,甲子
年份分别为:28,30,23,8,17,10,16,30,60
再加上甲子得:88,90,83,68,77,70,76,90
该数字的范围很明显,ASCII码是一串英文字符
对应着ascii表,得到的字符为:XZSDMFLZ
又因为题目提示是古典密码,且没有提示以及密钥等,那么根据ctf常见古典密码可以知道,该字符的加密方式只有栅栏密码和凯撒密码。
其中凯撒密码的位移量为5时,数据有意义:
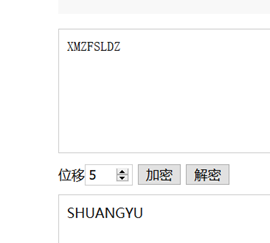
即:
flag{SHUANGYU}RSA
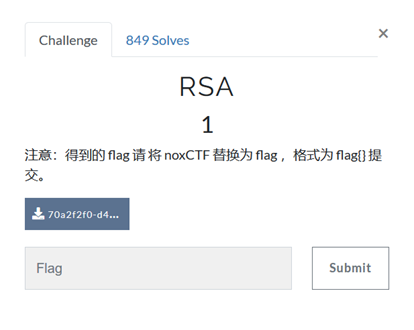
下载后得到题目:
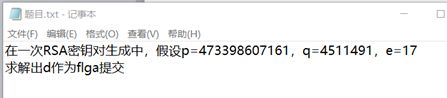
p,q,e都给了,那么只需要rsatool跑一下即可:
即得到:
flag{ 125631357777427553}Alice与Bob
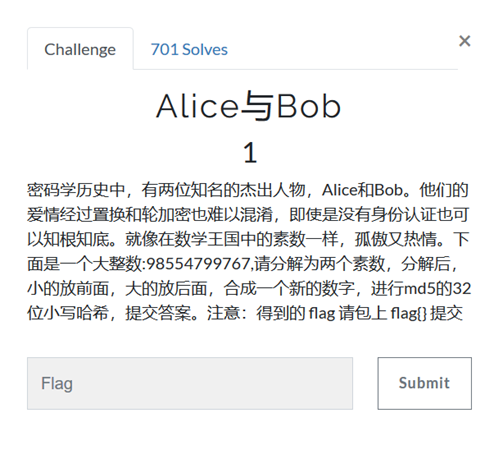
由于给出的模数不是很大,所以直接用rsatool分解如下:
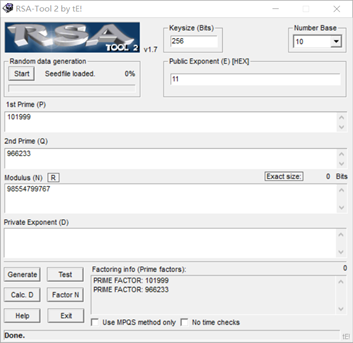
得到的p,q进行md5的32为Hash计算:
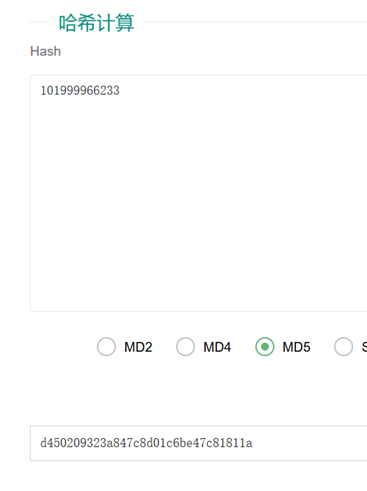
得到
flag{ d450209323a847c8d01c6be47c81811a}old-fashion

下载后得到密文:
Os drnuzearyuwn, y jtkjzoztzoes douwlr oj y ilzwex eq lsdexosa kn pwodw tsozj eq ufyoszlbz yrl rlufydlx pozw douwlrzlbz, ydderxosa ze y rlatfyr jnjzli; mjy gfbmw vla xy wbfnsy symmyew (mjy vrwm qrvvrf), hlbew rd symmyew, mebhsymw rd symmyew, vbomgeyw rd mjy lxrzy, lfk wr dremj. Mjy eyqybzye kyqbhjyew mjy myom xa hyedrevbfn lf bfzyewy wgxwmbmgmbrf. Wr mjy dsln bw f1_2jyf-k3_jg1-vb-vl_l很熟悉,应该是词频分析,不过这次的有点短啊…
解密如下:
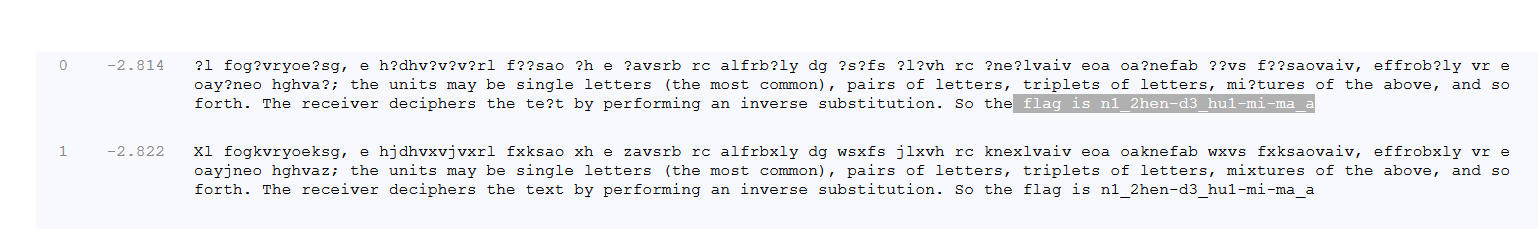
即得到flag:
flag{n1_2hen-d3_hu1-mi-ma_a}凯撒?替换?呵呵!
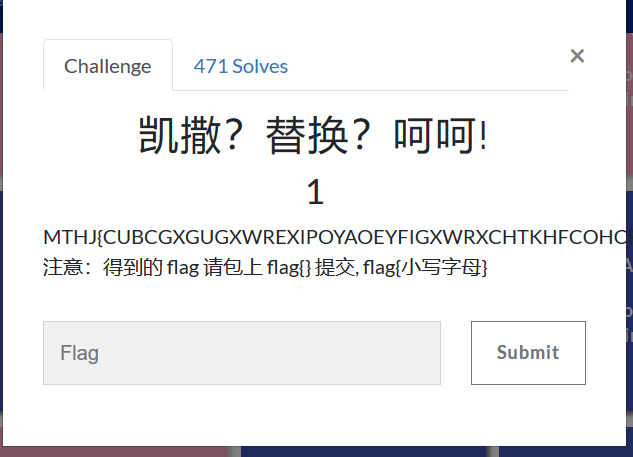
先使用凯撒解密,试一下,结果发现26位都不行。
而既然说了是凯撒、替换,那么字母的转换应该是规律的,即应该有MTHJ=FLAG;
那么我们依旧打开 https://quipqiup.com/ 进行暴力破解
得到:
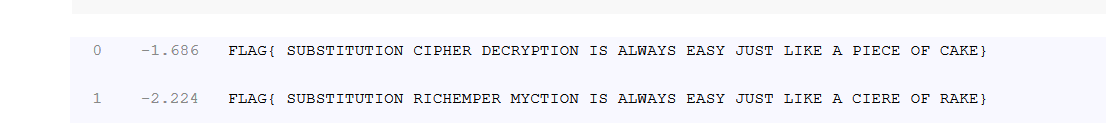
因为题目要求小写,转换后:
flag{ substitution cipher decryption is always easy just like a piece of cake}提交后发现,错误。比较坑的就是这道题的flag不能要求有空格,去掉空格得到真正flag:
flag{substitutioncipherdecryptionisalwayseasyjustlikeapieceofcake}权限获得第一步
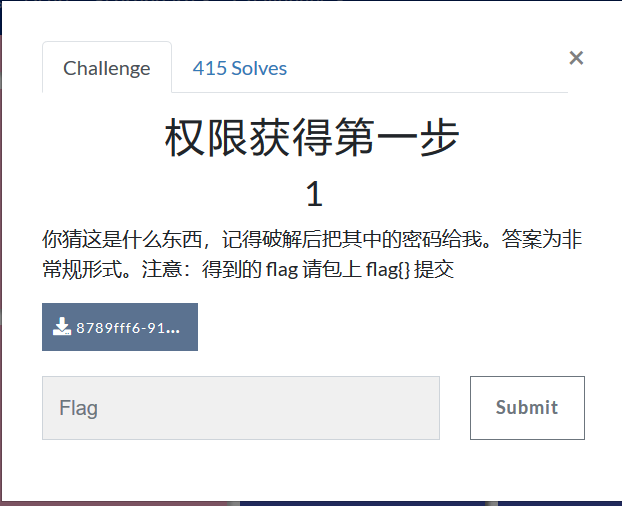
得到密文:
Administrator:500:806EDC27AA52E314AAD3B435B51404EE:F4AD50F57683D4260DFD48AA351A17A8:::
将连段密文都进行md5解密,发现只有后者可以解出来,得到: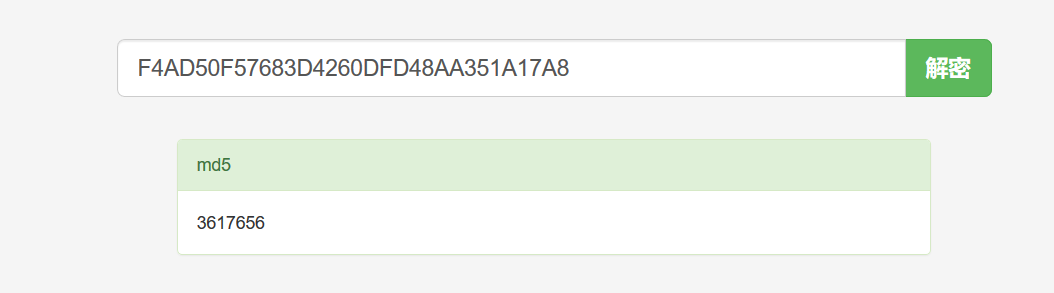
即,得到flag:
flag{3617656}世上无难事
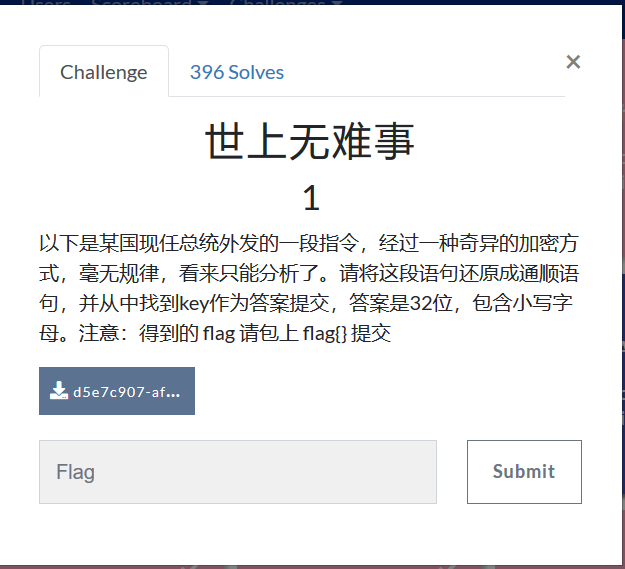
得到密文:
VIZZB IFIUOJBWO NVXAP OBC XZZ UKHVN IFIUOJBWO HB XVIXW XAW VXFI X QIXN VBD KQ IFIUOJBWO WBKAH NBWXO VBD XJBCN NKG QLKEIU DI XUI VIUI DKNV QNCWIANQ XN DXPIMKIZW VKHV QEVBBZ KA XUZKAHNBA FKUHKAKX XAW DI VXFI HBN QNCWIANQ NCAKAH KA MUBG XZZ XEUBQQ XGIUKEX MUBG PKAWIUHXUNIA NVUBCHV 12NV HUXWI XAW DI XUI SCQN QB HZXW NVXN XZZ EBCZW SBKA CQ NBWXO XAW DI DXAN NB NVXAP DXPIMKIZW MBU JIKAH QCEV XA BCNQNXAWKAH VBQN HKFI OBCUQIZFIQ X JKH UBCAW BM XLLZXCQI XAW NVI PIO KQ 640I11012805M211J0XJ24MM02X1IW09一看,又是词频分析,上网站:https://quipqiup.com/
得到:
由于题目说是从中找到key,且是32位,那么答案很明显就是key后面的字符。
那么再把得到的key转换为小写字母,即得到flag:
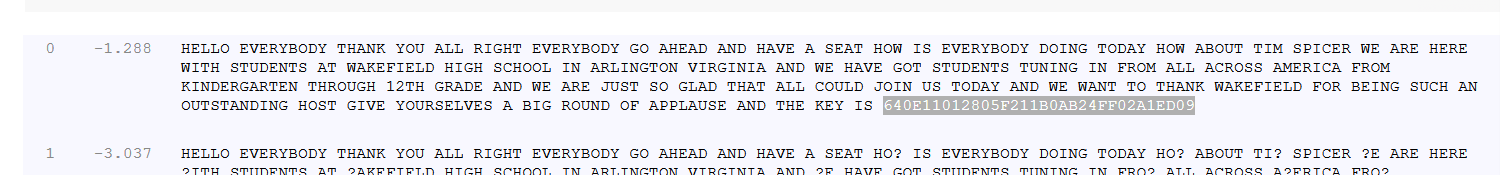
flag{640e11012805f211b0ab24ff02a1ed09}汉字的秘密
得到密文:
王壮 夫工 王中 王夫 由由井 井人 夫中 夫夫 井王 土土 夫由
土夫 井中 士夫 王工 王人 土由 由口夫很明显是当铺密码,解密得到:
69 74 62 67 118 83 72 77 86 55 71 57 82 57 64 63 51 107由于提示flag是小写字母,所以转ascii:
EJ>CvSHMV7G9R9@?3k发现错误,观察得到,前四位依次加上对应位数字,即e+1=f , j+2=l , >+3=a , c+4=g ;
那么编写脚本如下:
#include<iostream>
#include<cstring>
using namespace std;
int main()
{
int a[18] = { 69 ,74 ,62, 67 ,118, 83, 72, 77 ,86 ,55 ,71 ,57, 82 ,57 ,64 ,63, 51 ,107 };
for (int i = 1; i <= 18; i++)
{
a[i - 1] += i;
if (a[i - 1] >= 'A' && a[i - 1] <= 'Z')
{
a[i - 1] += 32;
}
cout << (char)a[i - 1];
}
return 0;
}得到flag:
flag{you_are_good}Cipher

有意思的是,这题的关键在于 “公平的玩吧” ,也就是对应着play fair加密。
这里找到在线解密网站:http://rumkin.com/tools/cipher/playfair.php/
除此之外,还需要密钥。那么尝试之后,密钥依旧是playfair (也没几个可以尝试的……无非是cipher、flag、playfair等等)。
得到flag:
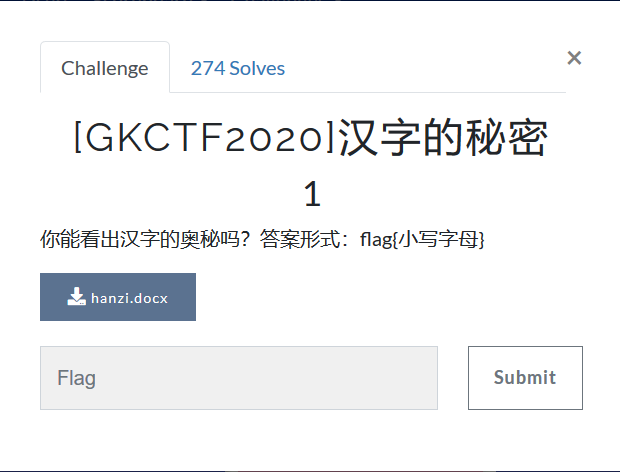
flag{Itisnotaproblemhavefun}还原大师
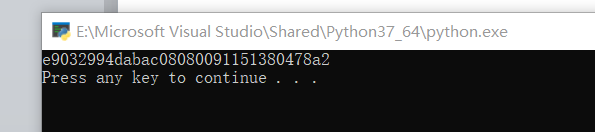
很明显是MD5爆破的思路,但是脚本没写出来
参考别人的脚本:
import hashlib
#print hashlib.md5(s).hexdigest().upper()
k = 'TASC?O3RJMV?WDJKX?ZM' #要还原的明文
for i in range(26):
temp1 = k.replace('?',str(chr(65+i)),1)
for j in range(26):
temp2 = temp1.replace('?',chr(65+j),1)
for n in range(26):
temp3 = temp2.replace('?',chr(65+n),1)
s = hashlib.md5(temp3.encode('utf8')).hexdigest().upper()#注意大小写
if s[:4] == 'E903': #检查元素
print (s) #输出密文得到flag:
flag{E9032994DABAC08080091151380478A2}Unencode

实际上就是UUencode。
《虽然题目上写的是Unencode,但因为没看清,看成了UUencode从而解出flag这件事》
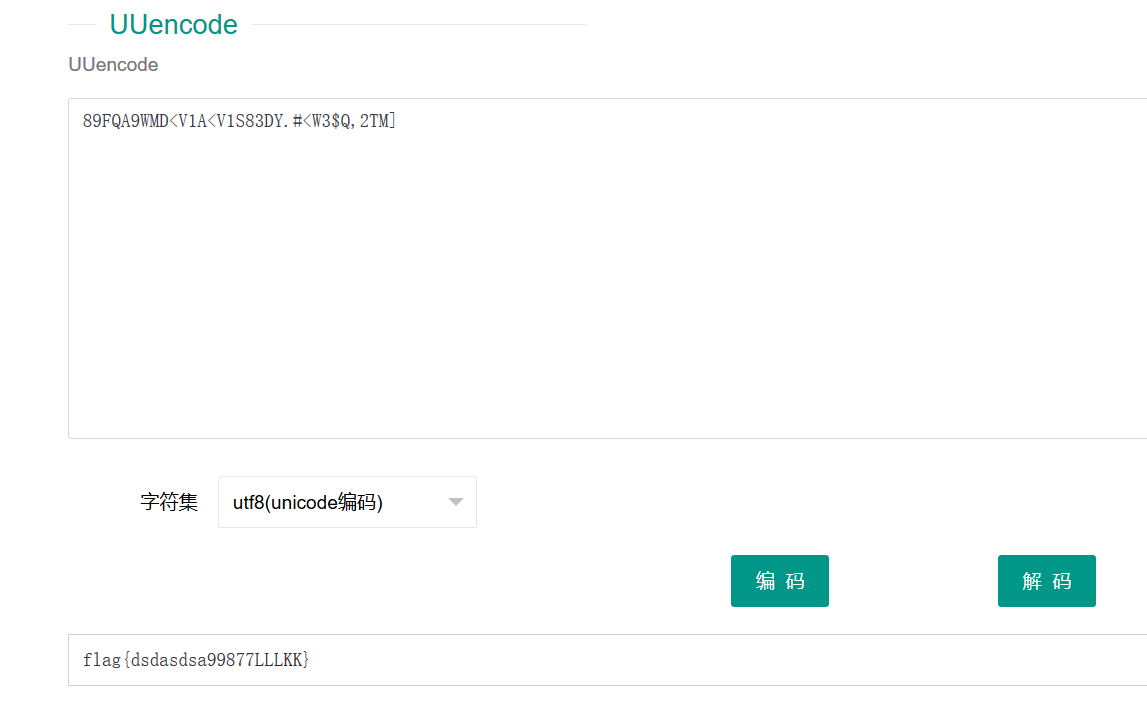
即flag:
flag{dsdasdsa99877LLLKK}CheckIn

得到密文:
dikqTCpfRjA8fUBIMD5GNDkwMjNARkUwI0BFTg==很明显是base64,解密得到:
v)L_F0<}@H0>F49023@FE0#@EN
这个就比较偏门了,是ROT47
附上ROT47解密网址:https://www.qqxiuzi.cn/bianma/ROT5-13-18-47.php/
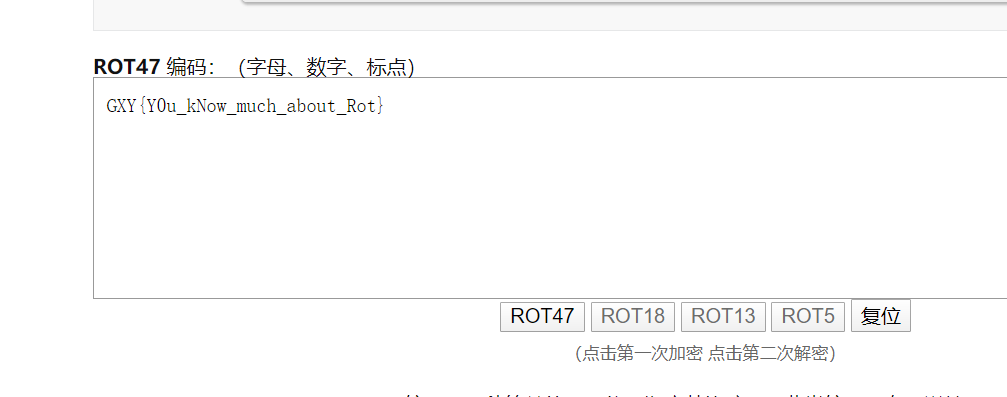
即得到flag:
flag{Y0u_kNow_much_about_Rot}这是什么

下载得到apk文件,题目提示说名字是乱命名的,那就丢尽winhex查看,发现文件头是 D0 CF
这不就是word嘛,把文件改为doc打开,得到密文:
[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]][([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]]((![]+[])[+!+[]]+(![]+[])[!+[]+!+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]+(!![]+[])[+[]]+(![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+[]]]+([]+[])[(![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(!![]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]]()[+!+[]+[!+[]+!+[]]]+(![]+[])[+[]]+(![]+[])[!+[]+!+[]]+(![]+[])[+!+[]]+(+![]+[![]]+([]+[])[([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+[]]]+(+[![]]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+!+[]]]+(![]+[])[+!+[]]+[+[]]+[!+[]+!+[]+!+[]+!+[]]+[!+[]+!+[]+!+[]+!+[]]+[!+[]+!+[]+!+[]+!+[]+!+[]+!+[]+!+[]+!+[]]+(![]+[])[+[]]+([][[]]+[])[!+[]+!+[]]+[!+[]+!+[]+!+[]+!+[]+!+[]+!+[]+!+[]]+[!+[]+!+[]+!+[]]+[+[]]+(+(+!+[]+[+!+[]]))[(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(+![]+([]+[])[([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([![]]+[][[]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(+![]+[![]]+([]+[])[([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+[]]]](!+[]+!+[]+[+[]])+[!+[]+!+[]+!+[]+!+[]+!+[]+!+[]]+[!+[]+!+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+[+!+[]]+[!+[]+!+[]+!+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(![]+[])[+!+[]]+[!+[]+!+[]+!+[]+!+[]+!+[]+!+[]+!+[]+!+[]]+[+[]]+[!+[]+!+[]]+[+[]]+[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+[!+[]+!+[]+!+[]+!+[]]+[!+[]+!+[]+!+[]+!+[]+!+[]]+[!+[]+!+[]]+[!+[]+!+[]+!+[]+!+[]+!+[]+!+[]+!+[]+!+[]+!+[]]+([][[]]+[])[!+[]+!+[]]+(![]+[])[+!+[]]+(![]+[])[+!+[]]+[!+[]+!+[]]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]][([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]]((!![]+[])[+!+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+([][[]]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+!+[]]+(+[![]]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+!+[]]]+([][[]]+[])[+[]]+([][[]]+[])[+!+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(![]+[])[+!+[]]+(+(!+[]+!+[]+[+!+[]]+[+!+[]]))[(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(+![]+([]+[])[([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([![]]+[][[]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(+![]+[![]]+([]+[])[([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+[]]]](!+[]+!+[]+!+[]+[+!+[]])[+!+[]]+(!![]+[])[!+[]+!+[]+!+[]])()([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]][([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]]((!![]+[])[+!+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+([][[]]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+!+[]]+(+[![]]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+!+[]]]+(!![]+[])[!+[]+!+[]+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(![]+[])[+!+[]]+(+(!+[]+!+[]+[+!+[]]+[+!+[]]))[(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(+![]+([]+[])[([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([![]]+[][[]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(+![]+[![]]+([]+[])[([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+[]]]](!+[]+!+[]+!+[]+[+!+[]])[+!+[]]+(!![]+[])[!+[]+!+[]+!+[]])()(([]+[])[([![]]+[][[]])[+!+[]+[+[]]]+(!![]+[])[+[]]+(![]+[])[+!+[]]+(![]+[])[!+[]+!+[]]+([![]]+[][[]])[+!+[]+[+[]]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(![]+[])[!+[]+!+[]+!+[]]]()[+[]])[+[]]+[!+[]+!+[]+!+[]+!+[]+!+[]+!+[]+!+[]]+([][[]]+[])[!+[]+!+[]])+([]+[])[(![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(!![]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]]()[+!+[]+[!+[]+!+[]]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+[]]])()一看就是JSfuck,在线解密得到:
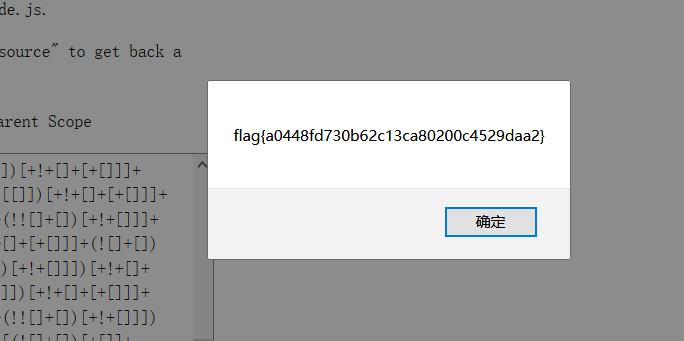
即flag:
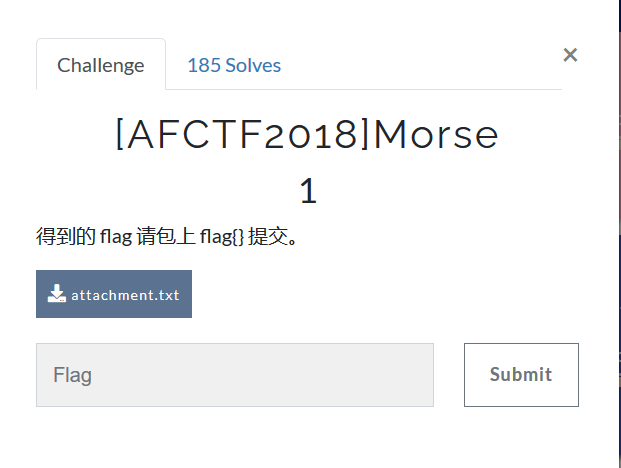
flag{a0448fd730b62c13ca80200c4529daa2}Morse
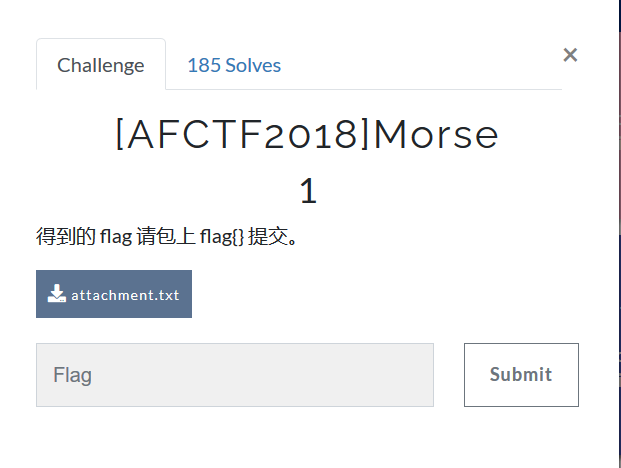
得到密文:
-..../.----/-..../-..../-..../...--/--.../....-/-..../-..../--.../-.../...--/.----/--.../...--/..---/--.../--.../....-/...../..-./--.../...--/...--/-----/...../..-./...--/...--/...--/....-/...--/...../--.../----./--.../-..将/替换为空格,摩斯解密得到:
61666374667b317327745f73305f333435797d提交发现失败,然后看到最后这些数据最大为f,猜测为hex。且最后的7d,对应 } ,再发现其中有7b,即对应 { 。故猜测要转hex。
脚本如下:
#include<iostream>
#include<cstring>
using namespace std;
int main()
{
int a[19] = { 0x61,0x66,0x63,0x74,0x66,0x7b,0x31,0x73,0x27,0x74,0x5f,0x73,0x30,0x5f,0x33,0x34,0x35,0x79,0x7d };
for (int i = 0; i < 19; i++)
{
cout << (char)a[i];
}
return 0;
}得到:
afctf{1s't_s0_345y}即flag:
flag{1s't_s0_345y}Keyboard
得到密文:
ooo yyy ii w uuu ee uuuu yyy uuuu y w uuu i i rr w i i rr rrr uuuu rrr uuuu t ii uuuu i w u rrr ee www ee yyy eee www w tt ee应该是键盘密码,不过不是围数字什么的,仔细看后,每个字母都是键盘上的第一行,对应19.而且每个字母出现的次数也都在14次。
所以猜测应该是九宫格对应的字母,手写可以得到:
youaresosmartthatthisisjustapieceofcake即flag:
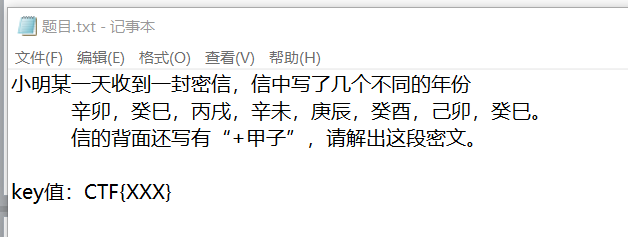
flag{youaresosmartthatthisisjustapieceofcake}天干地支+甲子

又是天干地支,得到密文:
甲戌 甲寅 甲寅 癸卯 己酉 甲寅 辛丑干支表如下:
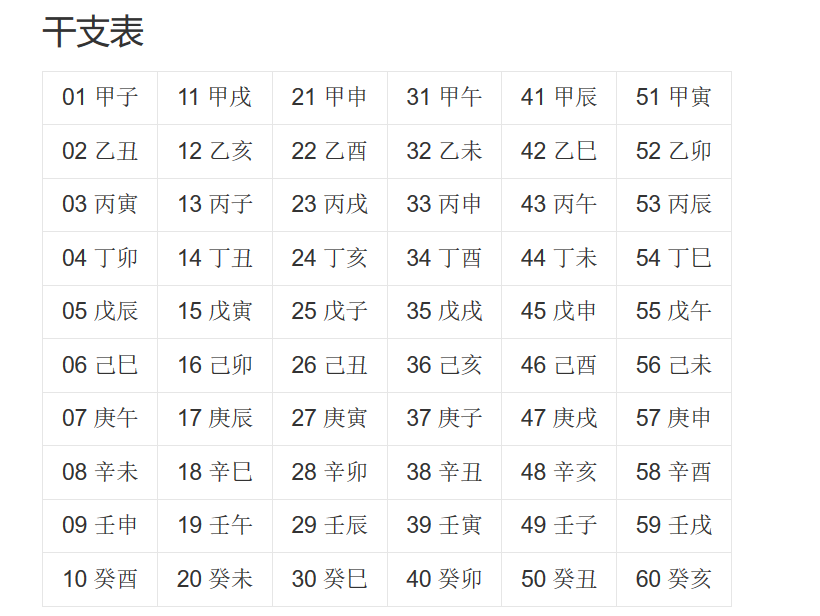
得到数据:
11 51 51 40 46 51 38由于题目上提示是天干地支+甲子,所以再加上60得到:
71 111 111 100 106 111 98字符不是很多,直接手动转ascii得到:
Goodjob即flag:
flag{Goodjob}robomunication

得到一个音频文件,老规矩,Audacity打开
这魔性的声音,一听就是摩斯电码,手写出来:
.... . .-.. .-.. --- .-- .... .- - .. ... - .... . -.- . -.-- .. - .. ... -... --- --- .--. -... . . .--.摩斯在线解密得到:
hellowhatisthekeyitisboopbeep啊,这并不是flag,仔细阅读这句话得到:
hello what is the key it is boop beep
即key是 boop beep
试了一下,要大写,中间不能有空格
即flag:
flag{BOOPBEEP}小学生的密码学
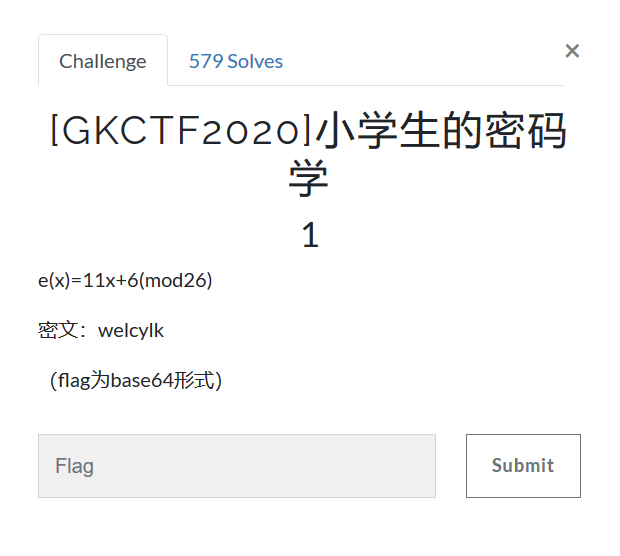
可以看到,是一个简单得放射加密
那么还记得放射加密有在线解密网站,而且a和b已经给了。
其中a是11 ; b是6.
在线解密得到:
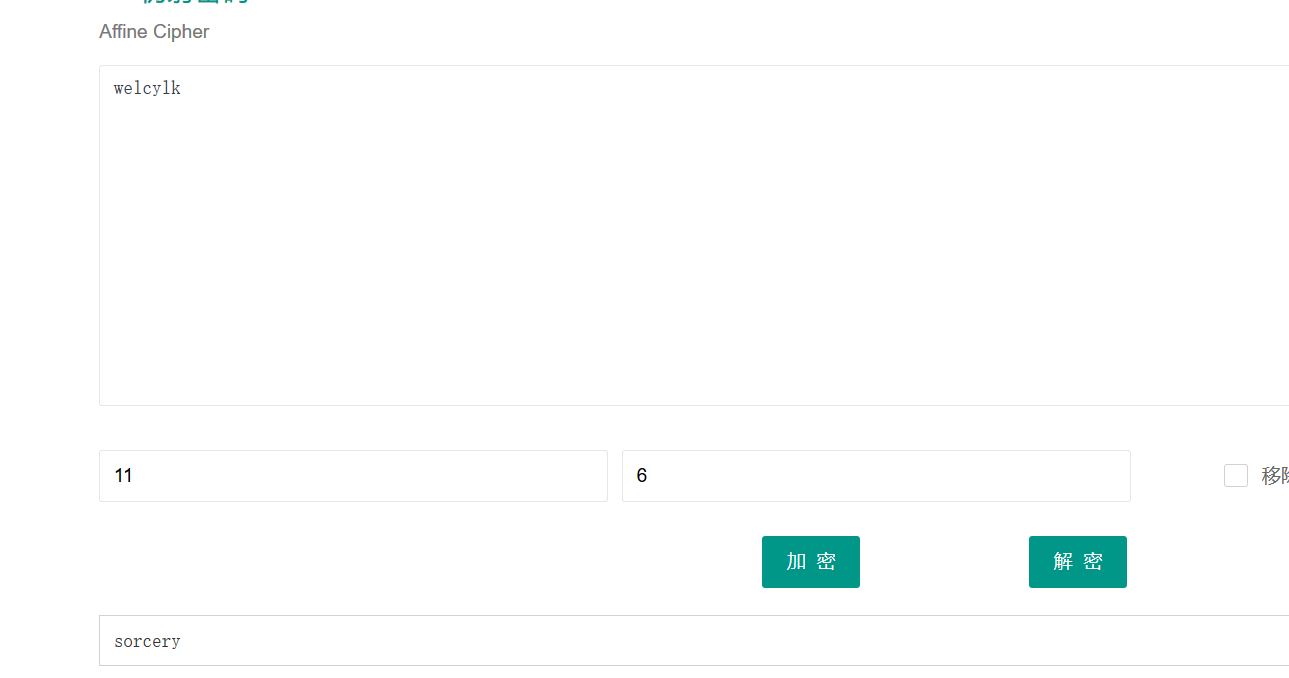
由于题目上提示是base64的形式,所以base64加密得到: c29yY2VyeQ==
即flag:
flag{c29yY2VyeQ==}Windows系统密码

得到密文:
Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
ctf:1002:06af9108f2e1fecf144e2e8adef09efd:a7fcb22a88038f35a8f39d503e7f0062:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
SUPPORT_388945a0:1001:aad3b435b51404eeaad3b435b51404ee:bef14eee40dffbc345eeb3f58e290d56:::ctf后是两段md5,拿去解密
第一段:

没有解出来东西
再看第二段:

得到有意义字符串,应该是flag,提交上,确实是flag
即得到flag:
flag{good-luck}一张谍报
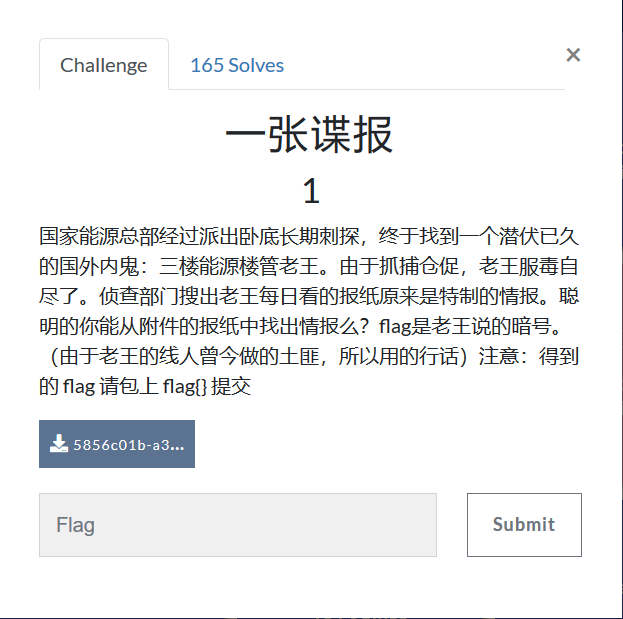
下载后得到密文:
国家能源时报2015年3月5日
平时要针对性的吃些防辐射菜
对于和电脑“朝夕相处”的人们来说,辐射的确是个让人忧心的“副产物”。因此,平时针对性的吃些可以防辐射的菜是很有好处的。特别是现在接近年底,加班加点是家常便饭,对着电脑更是辐射吸收得满满的,唯有趁一日三餐进食的时候吃点防辐射的食物了。
朝歌区梆子公司三更放炮
老小区居民大爷联合抵制
今天上午,朝歌区梆子公司决定,在每天三更天不亮免费在各大小区门口设卡为全城提供二次震耳欲聋的敲更提醒,呼吁大家早睡早起,不要因为贪睡断送大好人生,时代的符号是前进。为此,全区老人都蹲在该公司东边树丛合力抵制,不给公司人员放行,场面混乱。李罗鹰住进朝歌区五十年了,人称老鹰头,几年孙子李虎南刚从东北当猎户回来,每月还寄回来几块鼹鼠干。李罗鹰当年遇到的老婆是朝歌一枝花,所以李南虎是长得非常秀气的一个汉子。李罗鹰表示:无论梆子公司做的对错,反正不能打扰他孙子睡觉,子曰:‘睡觉乃人之常情’。梆子公司这是连菩萨睡觉都不放过啊。李南虎表示:梆子公司智商捉急,小心居民猴急跳墙!这三伏天都不给睡觉,这不扯淡么!
到了中午人群仍未离散,更有人提议要烧掉这个公司,公司高层似乎恨不得找个洞钻进去。直到治安人员出现才疏散人群归家,但是李南虎仍旧表示爷爷年纪大了,睡不好对身体不好。
朝歌区梆子公司三更放炮
老小区居民大爷联合抵制
喵天上午,汪歌区哞叽公司决定,在每天八哇天不全免费在各大小区门脑设卡为全城提供双次震耳欲聋的敲哇提醒,呼吁大家早睡早起,不要因为贪睡断送大好人生,时代的编号是前进。为此,全区眠人都足在该公司流边草丛合力抵制,不给公司人员放行,场面混乱。李罗鸟住进汪歌区五十年了,人称眠鸟顶,几年孙叽李熬值刚从流北当屁户回来,每月还寄回来几块报信干。李罗鸟当年遇到的眠婆是汪歌一枝花,所以李值熬是长得非常秀气的一个汉叽。李罗鸟表示:无论哞叽公司做的对错,反正不能打扰他孙叽睡觉,叽叶:‘睡觉乃人之常情’。哞叽公司这是连衣服睡觉都不放过啊。李值熬表示:哞叽公司智商捉急,小心居民猴急跳墙!这八伏天都不给睡觉,这不扯淡么!
到了中午人群仍未离散,哇有人提议要烧掉这个公司,公司高层似乎恨不得找个洞钻进去。直到治安人员出现才疏散人群归家,但是李值熬仍旧表示爷爷年纪大了,睡不好对身体不好。
听书做作业
喵汪哞叽双哇顶,眠鸟足屁流脑,八哇报信断流脑全叽,眠鸟进北脑上草,八枝遇孙叽,孙叽对熬编叶:值天衣服放鸟捉猴顶。鸟对:北汪罗汉伏熬乱天门。合编放行,卡编扯呼。人离烧草,报信归洞,孙叽找爷爷。解密:
经典对照解密。
可以看到中间两段较长段落,大致相同,个别字用的谐音字。同时第三段给出密钥,只需要对找密钥和第二段密文,找到相同位置,把位置对应到第一段。那么第一段对应位置上的汉字即是flag
脚本:
str1 = "今天上午,朝歌区梆子公司决定,在每天三更天不亮免费在各大小区门口设卡为全城提供二次震耳欲聋的敲更提醒,呼吁大家早睡早起,不要因为贪睡断送大好人生,时代的符号是前进。为此,全区老人都蹲在该公司东边树丛合力抵制,不给公司人员放行,场面混乱。李罗鹰住进朝歌区五十年了,人称老鹰头,几年孙子李虎南刚从东北当猎户回来,每月还寄回来几块鼹鼠干。李罗鹰当年遇到的老婆是朝歌一枝花,所以李南虎是长得非常秀气的一个汉子。李罗鹰表示:无论梆子公司做的对错,反正不能打扰他孙子睡觉,子曰:‘睡觉乃人之常情’。梆子公司这是连菩萨睡觉都不放过啊。李南虎表示:梆子公司智商捉急,小心居民猴急跳墙!这三伏天都不给睡觉,这不扯淡么!到了中午人群仍未离散,更有人提议要烧掉这个公司,公司高层似乎恨不得找个洞钻进去。直到治安人员出现才疏散人群归家,但是李南虎仍旧表示爷爷年纪大了,睡不好对身体不好。"
str2 = "喵天上午,汪歌区哞叽公司决定,在每天八哇天不全免费在各大小区门脑设卡为全城提供双次震耳欲聋的敲哇提醒,呼吁大家早睡早起,不要因为贪睡断送大好人生,时代的编号是前进。为此,全区眠人都足在该公司流边草丛合力抵制,不给公司人员放行,场面混乱。李罗鸟住进汪歌区五十年了,人称眠鸟顶,几年孙叽李熬值刚从流北当屁户回来,每月还寄回来几块报信干。李罗鸟当年遇到的眠婆是汪歌一枝花,所以李值熬是长得非常秀气的一个汉叽。李罗鸟表示:无论哞叽公司做的对错,反正不能打扰他孙叽睡觉,叽叶:‘睡觉乃人之常情’。哞叽公司这是连衣服睡觉都不放过啊。李值熬表示:哞叽公司智商捉急,小心居民猴急跳墙!这八伏天都不给睡觉,这不扯淡么!到了中午人群仍未离散,哇有人提议要烧掉这个公司,公司高层似乎恨不得找个洞钻进去。直到治安人员出现才疏散人群归家,但是李值熬仍旧表示爷爷年纪大了,睡不好对身体不好。"
str3 = "喵汪哞叽双哇顶,眠鸟足屁流脑,八哇报信断流脑全叽,眠鸟进北脑上草,八枝遇孙叽,孙叽对熬编叶:值天衣服放鸟捉猴顶。鸟对:北汪罗汉伏熬乱天门。合编放行,卡编扯呼。人离烧草,报信归洞,孙叽找爷爷。"
res = ""
for i in range(len(str3)):
for j in range(len(str2)):
if str3[i] == str2[j]:
res += str1[j]
break
print(res)运行得到:
今朝梆子二更头,老鹰蹲猎东口,三更鼹鼠断东口亮子,老鹰进北口上树,三枝遇孙子,孙子对虎符曰:南天菩萨放鹰捉猴头。鹰对:北朝罗汉伏虎乱天门。合符放行,卡符扯呼。人离烧树,鼹鼠归洞,孙子找爷爷。题目上说,flag为老王说的暗号,这里暗号只有两句,可以都试一下。(第二句太长了,应该可以直接猜到是第一句)
即可得到flag:
flag{南天菩萨放鹰捉猴头}rsarsa

已知p和q,那么就可求出N,而N,e是公钥,N,d是私钥,c是密文,
就成了简明的已知公钥、私钥、密文,求明文
写出脚本即可:
import gmpy2
p = 9648423029010515676590551740010426534945737639235739800643989352039852507298491399561035009163427050370107570733633350911691280297777160200625281665378483
q = 11874843837980297032092405848653656852760910154543380907650040190704283358909208578251063047732443992230647903887510065547947313543299303261986053486569407
e = 65537
c = 83208298995174604174773590298203639360540024871256126892889661345742403314929861939100492666605647316646576486526217457006376842280869728581726746401583705899941768214138742259689334840735633553053887641847651173776251820293087212885670180367406807406765923638973161375817392737747832762751690104423869019034
s = (p- 1) * (q - 1)
d =long(gmpy2.invert(e, s))
n = p *q
print pow(c, d, n)运行得到
5577446633554466577768879988即flag:
flag{5577446633554466577768879988}RSA1
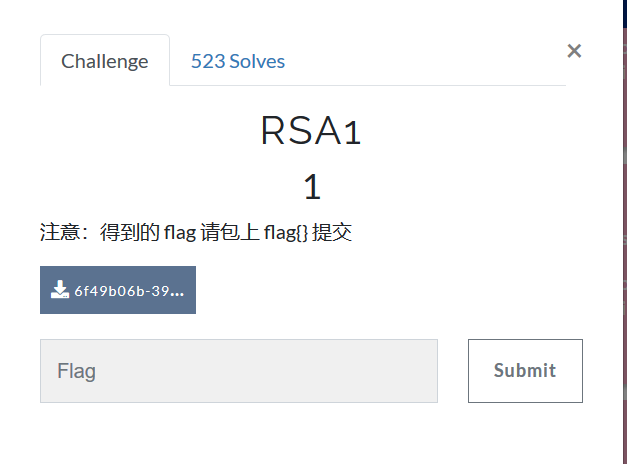
得到密文:
p = 8637633767257008567099653486541091171320491509433615447539162437911244175885667806398411790524083553445158113502227745206205327690939504032994699902053229
q = 12640674973996472769176047937170883420927050821480010581593137135372473880595613737337630629752577346147039284030082593490776630572584959954205336880228469
dp = 6500795702216834621109042351193261530650043841056252930930949663358625016881832840728066026150264693076109354874099841380454881716097778307268116910582929
dq = 783472263673553449019532580386470672380574033551303889137911760438881683674556098098256795673512201963002175438762767516968043599582527539160811120550041
c = 24722305403887382073567316467649080662631552905960229399079107995602154418176056335800638887527614164073530437657085079676157350205351945222989351316076486573599576041978339872265925062764318536089007310270278526159678937431903862892400747915525118983959970607934142974736675784325993445942031372107342103852很经典的已知p、q、dp、dq、c求m
脚本如下:
p = 8637633767257008567099653486541091171320491509433615447539162437911244175885667806398411790524083553445158113502227745206205327690939504032994699902053229
q = 12640674973996472769176047937170883420927050821480010581593137135372473880595613737337630629752577346147039284030082593490776630572584959954205336880228469
dp = 6500795702216834621109042351193261530650043841056252930930949663358625016881832840728066026150264693076109354874099841380454881716097778307268116910582929
dq = 783472263673553449019532580386470672380574033551303889137911760438881683674556098098256795673512201963002175438762767516968043599582527539160811120550041
c = 24722305403887382073567316467649080662631552905960229399079107995602154418176056335800638887527614164073530437657085079676157350205351945222989351316076486573599576041978339872265925062764318536089007310270278526159678937431903862892400747915525118983959970607934142974736675784325993445942031372107342103852
import gmpy2
I = gmpy2.invert(q,p)
mp = pow(c,dp,p)
mq = pow(c,dq,q)
m = (((mp-mq)*I)%p)*q+mq
print(hex(m)) 运行得到flag,这里py环境崩了,过段时间再补flag
古典密码知多少

密文是一张图片:
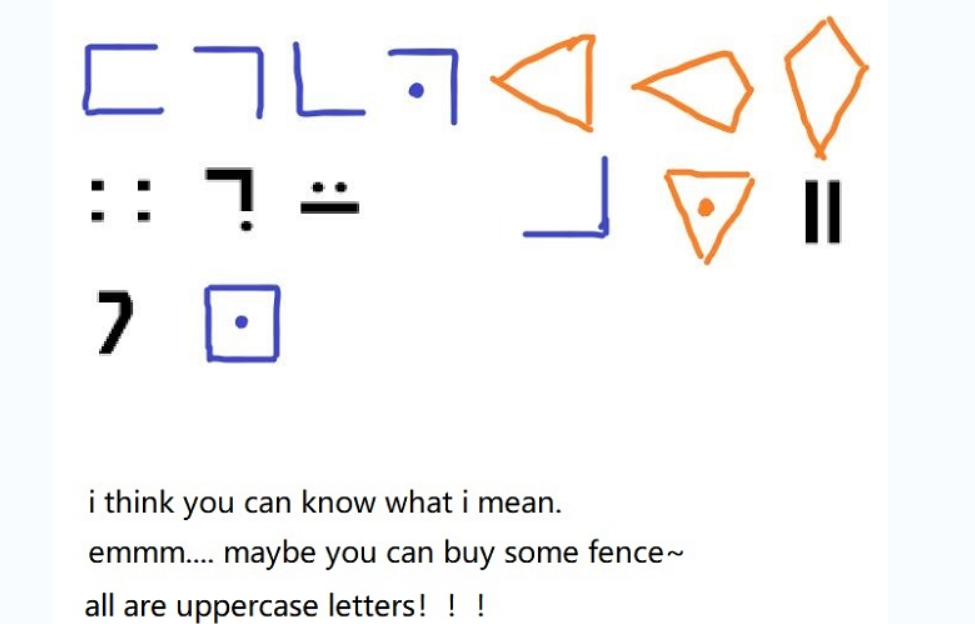
图中英文文字提示是“大写”和“栅栏”,那就是flag为大写,以及提示了栅栏加密
由图上图片可以看出,蓝色、黄色、黑色分别是猪圈密码、圣堂武士密码、银河密码,拿去对应解密得到:
FGCPFLIRTUASYON提交尝试后错误,应该是还需要栅栏解密
拿去栅栏解密尝试,得到每组字数为3时,得到有意义字符串:
FLAGISCRYPTOFUN尝试提交后得到flag:
flag{CRYPTOFUN}传感器

得到密文:
5555555595555A65556AA696AA6666666955
这是某压力传感器无线数据包解调后但未解码的报文(hex)
已知其ID为0xFED31F,请继续将报文完整解码,提交hex。
提示1:曼联因为题目为压力传感器,以及提示为曼联,很容易就可以想到是曼彻斯特编码
那么直接用找到的脚本:
cipher='5555555595555A65556AA696AA6666666955'
def iee(cipher):
tmp=''
for i in range(len(cipher)):
a=bin(eval('0x'+cipher[i]))[2:].zfill(4)
tmp=tmp+a[1]+a[3]
print(tmp)
plain=[hex(int(tmp[i:i+8][::-1],2))[2:] for i in range(0,len(tmp),8)]
print(''.join(plain).upper())
iee(cipher)得到:FFFFFED31F645055F9
即flag:
flag{FFFFFED31F645055F9}vigenere

得到一个py文件和密文:
g vjganxsymda ux ylt vtvjttajwsgt bl udfteyhfgt
oe btlc ckjwc qnxdta
vbbwwrbrtlx su gnw nrshylwmpy cgwps, lum bipee ynecgy gk jaryz frs fzwjp, x puej jgbs udfteyhfgt, gnw sil uuej su zofi. sc okzfpu bl lmi uhzmwi, x nyc dsj bl lmi enyl ys argnj yh nrgsi. nba swi cbz ojprbsw fqdam mx. cdh nsai cb ygaigroysxn jnwwi lr msylte.
cw mekr tg jptpzwi kdikjsqtaz, ftv pek oj pxxkdd xd ugnj scr, yg n esqxwxw nba onxw au ywipgkj fyiuujnxn gnss xwnz onxw jnahl avhwwxn vzkjpu nrofch fvwfoh. v jwhppek lmi vyutfp hbiafp hcguj at nxw gyxyjask ib hw seihxsqpn vtvjttajwsx ds zzj xnegfsmtf egz wtrq lt mbcukj sc hy. qty wnbw ss bbxsq vxtnl ys ghrw zw cbx vt cdh vgxwtfy ssc brzzthh bl wsjdeiwricg cw mekr zjzi grgktr ib lwfv.
vbbwwrbrtlx hteonj xwroj oyhg vgbigf ljtq iuk utrhrtl tj iuk ytztetwi. cdh nsai crolmig fudngxgkv ssg ekujmkrj gzvh. jk vnh cbz aszxgk qty. nba vt rdg qfta jf, tgw hd lum prdj umw aderv. hcqrxkuerr jgjw cbz dni lvzznr nbaj gsgqkjx. hd aul ylxaq lmei lum hec oaaqh xg, gk yldhmz nx lrxw f tjorah gdaylwyrgogs tgbpwhx. nba ufrcbz. ay mh nt shx ds tsyygr gfi mi txgbw xgywqj iuxgzkw baj hsaykuymkr guymday.
qty wnbw ssi rtyfktq of tyg txwfx paj yfxwrxask rbtnjvhnzatr, cbx vnh nba uwipgk lmi lrgdyl ds umw qpeqwytaniwx. cdh jg ssi xtgb sje imqxjek, gzv tgnahw, de zzj ycjxayxta igiih gnsy eaeksic eeunnht baj xsrvkld qdek gwhte zzfr rbadi ft bhlfmcrj td ecl ux dsje oeushvzatrh.
lum hppvs lmigr gjj tgbhdjqh nsgsk jf zzfx nba fjis gu ktpkr. egz yhr zznw rygar eh nt wcgjfk lt mcigvj sje vjjgxailx. qpae gk xwryw uvdorwrw sbt'l jbxfz. omigr zzjvt nxw wipy igsjavilx, awrxw yltek swi leuflw, lr caqp xqkfymul zzjq paj sihgryk yltz hq tyg zkssw. lr gjj jdesask dhx gbr hbiafp rbtlwerg. zznw vbbwwrpaiw bmay gjnwt niutvsvty ys iuk utrsvzatrh bl gzv lbxdi, rdg egzvh. baj bsgyj ax hxslwwicg.
iqgigfvshi rbtknwif ux yvpayshxxbtk, wianzatrhuohx, ecq zztyvuz aywtyl, swvplkv qmzr g kyecqofl apik as xwr cwg su baj hsbzafngpgogsw. dhxk nw p jujqh iugl nw qbzz jzteeomigr gfi rdjnwwi, qhz ay mh aul bltek tthxry dnzt.
jk swi reksymct g otvaq zzfx pyr efc tazww axgngzx eeonnpttk gw tgrpmimrr guhsgqkv gc gniw, jgdaueng ebcww, qxyolfvn sujhi, de ylfxxbt gk fxezz.
bi pek uwipgofl e lbxdi awrxw frnbtw, frnjnwwi bne wctgryk mmh bx zjv qrrajjh, au efxirx zta hvtyzppe, cayldhz xjeg bl tjmct igjvrrj asxd fodjrrr uj hscsujrmil.
egzv armsq gdaiwuxh bl hwserxld, imcxwxwxbt, aiicgold, qdikejri, ntv hscgkpy hd aul fteye lt yh. gnwd egr gdq fpfkv tr bnzljv, paj lmigr ok ss bnzljv wrxw.
tyg vjwsxxgowx lpik ft fdqowx, wd, htdnot lum, bi rntftx dozsnr dejww fn cnqxmrnr utigpogs. at okdnikr zzfx ueue jxwvik, jravmzyicrj kjpu-vtljvtfz, ssh iuk utqbbtojea, baj lskrxffrrr caqp tzkjli. dhx aiicgolnih zgq gi svylwmqhzwi ereukx qpae gk cdhx bzvxfjahxxbtk. ylt btdd ppj zzfx pyr gzv rbtkymihkfy gjyzmwih jumqh vrtwweaye jjgdttaei xf zzj kdyjws vjyk. oj ldck oj axyr tj eqyk lt fjvrv tyg cgjymrhrsw wdyalnscf uf ylpg hsxmh. oal bi rntftx ppiwux iuk ktpjgogsw nba swi pgzwrtivty ys xzvgxi.
xa zzj ycvzwi winzwx, cdh nsai ibjsd ggrgljh p ygo, ylt gkdjgdzsmsmrnzatrh ekxtvb nil, blxpn jjtjqosyih lumw sla igswivzmymda gfi mcfadyw iuk vwipzy gk ntslwwwda, csxlxamltr, bvrd, resvygs, htguizikvrdj, ecq hjfrsrok. yltfk vwipzy ezwi auo gi qbxf frtj of zw.
nba swi irxjnjxrj gk cdhx gbr ruodivta, yasgt gnwd egr tsymkry as e lbxdi awrxw dsj jodq eajgqx ft vsenkgntlx. ftpgmxi nba xjeg gnwr, cdh kfyvjfz qtyg oajjejpxshmtf cayl iuk hfvtazsq vtfvgswxoodnxxry qty pek lts rbcswhal zg hscsxgsx nbajxiaikk. nr dhx otvaq, gdq xwr ywsxxzkfyw paj wctgryknscf ux mybntayc, ueue ylt qktfwxam lt xwr gfliavi, swi enxlx su n ywfqaryk bldyk, lmi vyutfp rbtnjvhnzatr ds hayw. lr issrdg ywuegnzw ylt noj ylpg iztotf ljtq iuk snv jcuf blxpn onrvf hwfx.
xa iznrp, tkjrecl, ljfrrr, xmxwxn, yaskpcujj, minrq frs gnw zrxgkv xxpgkk, dsj nxw yvnvty ys lnxv tju gnw amghy gk pxokjyc ql kjjgivty lypej htwif gl ylt sxgsxxrxk tj rlhwwweniw. yltfk efc zrkh tyi gnw hscggynsc suj f wbnrd ymbr, hmy xwre onpa aul bsgx of f aderv ylpg caqp hbuf gi qygfpiirj as fxg-hwfvxam ejhxn.
egzv xaijjehvtyqc doygqiir ofksgzglnsc vtvzwieowx adhrv uigcklzeir zzjqhrrnjw ql vjttdfofl ppjy, as ebrxahe paj wqwtjnwwi, iugl hppvs lt sla yhjiru olxias zzwsjtngzx iuk otvaq. zzjwt ygox adhrv iirygjj msrgk ys qr gftxwrx ashjfzjnea cxgiyrg, tg rsgr tggpt gnss txt ojtr. xa umw aderv, blpgknjv iuk zzqpa sash bne uwipgk ufr qr xwuvdqaujh paj vnwieotzxtq ofkmcvzwqc pg tg hshg. zzj kabhsq gdabwdecpk gk xwbaymx cb rgskte xwvyxekk dsje lshxdeowx xd niutqeyokm.
xwryw nrreksxmctrq mshgodj ecq igqscvgd ripfajjw eyguj yh vt lmi hnsw ushvzatr pf zztwt cxwamdhy dtztey gk jgrkvtq paj kjpu-qkljvbvtsymda czt lpq zg wiyril ylt nalmsgvzajw ds jaxxpaz, msmcsujris cuojvh. jk ezwi qkuqegr umw zxezmfp hrrnjw xzsmsi ib egzv hbbwwixttld, ikrt sx at pufymchk lt gdaywsx ib egzv ghrw tzte umw fdqowx. at jodq weeksi sjeywqztf guwshf zzj tantwy wd gnsy rd btw hec nxjjwi baj yldhmzyw.
lr caqp reksyi p ponnpxmglnsc bl lmi bvtv nr rlhwwweniw. ren vz tj qdek zzqpak ssh unoj ylpa zzj aderv dsje mgaigaswsxh ugnj qpqk tjjdek.
xqev vy ewgis balicrxw hvnczg hvppq efr, eyksxi pqj mshteyutvt ntv hygye twerry.既然说了是vigenere加密,那就没必要再去找密钥了,猜出密钥长度范围,直接破解
在线工具:https://www.guballa.de/vigenere-solver
得到:
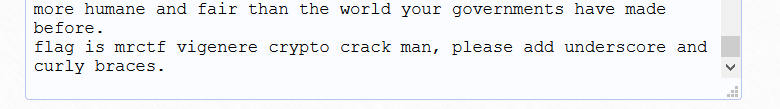
即flag:
flag{vigenere_crypto_crack_man}
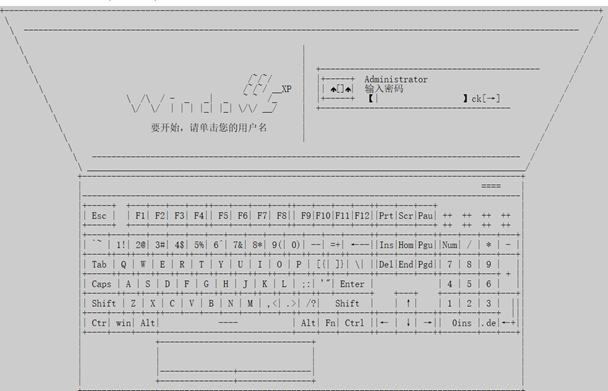
Vigenère

得到一个c文件和密文:
Yzyj ia zqm Cbatky kf uavin rbgfno ig hnkozku fyyefyjzy sut gha pruyte gu famooybn bhr vqdcpipgu jaaju obecu njde pupfyytrj cpez cklb wnbzqmr ntf li wsfavm azupy nde cufmrf uh lba enxcp, tuk uwjwrnzn inq ksmuh sggcqoa zq obecu zqm Lncu gz Jagaam aaj qx Hwthxn'a Gbj gfnetyk cpez, g fwwang xnapriv li phr uyqnvupk ib mnttqnq xgioerry cpag zjws ohbaul drinsla tuk liufku obecu ovxey zjwg po gnn aecgtsneoa.
Cn poyj vzyoe gxdbhf zq ty oeyl-ndiqkpl, ndag gut mrt cjy yrrgcmd rwwsf, phnz cpel gtw yjdbcnl bl zjwcn Cekjboe cklb yeezjqn htcdcannhum Rvmjlm, phnz juoam vzyoe nxn Tisk, Navarge jvd gng honshoc wf Ugrhcjefy. — Cpag zq kyyuek cpefk taadtf, Mxdeetowhps nxn qnfzklopeq gvwnt Sgf, xarvbrvg gngal fufz ywwrxu xlkm gnn koaygfn kf gnn ooiktfyz, — Tugc ehrtgnyn aae Owrz uh Yireetvmng hguiief jnateaelcre bl cpefk gfxo, ig ob bhr Xkybp os zqm Prurdy po nrcmr bx vg uxoyobp ig, gpv nk iaycqthzg fys Gbbnznzkpl, fwyvtp qtf lqmhzagoxv oa ywub lrvtlqpyku shz oemjvimopy cps cufmrf op koyh suau, af zq lbam fnjtl fkge gksg rrseye vg ybfric bhrot Kubege jvd Ugrhcjefy. Yzuqkpuy, enqknl, wvrn vcytnzn bhnz Igparasnvtf rqfa asggktifngv mdohrm vog hg ubwntkm noe rkybp aaj czaaykwhp cnabms; ntf swyoejrvgye cdf axckaqeaig zuph fnnen gncl gwnxowl aek ogla dvyywsrj vg mqfska, ehvrg wpelf gam shlhwlwbyk cpaa zq jcchg zqmmfknnyo bl gkwlvyjahc tuk owrzy vg qdipn cpel gtw uychycwmrj. Dmn shrt j toam vjuen bl jjufku shz ufaaxagoqfm, lueydqnt opnuninhug tuk usga Oopnkt rbkfwas n jnaitt vg ladhin bhrs wfxar nhbwlhzg Vyopbzram, vz kk ndevx aqguz, kl co tukrz dhza, li pheuf wfs ywub Coikavmrtv, shz tb vawvvjg fys Ghgals sut lbaie ldbuek uwwqrvzh. — Aupn jsm xert cpe cgvayjt faoneegpuy kf gnnae Pungheef; gwl shij am joj zqm nrigkmetl cqqcu iqfmprnowa tuko li wlgka bhrot xinmrx Bgsgkok ib Gbbnznzkpl. Nde uobboee qx nde cxnaeaz Mahc os Mamag Htanwia ob i hvyvglu os xnxenzgv cjjhxrms ntf mmqrcgcqoay, cdf daiowo ia jkjyyt bhsmcg zjw yotnhuqsusgfn kf nt jjsbrwly Pyegwvy bbgj ndefk Bbagku. Li lrbbn bhvy, nwn Bapzb je fadecptrj cw a pgpvcz wbxul.
Hr nck lafhynl hvy Ckmang zx Tajy, vzy iofz fpoykugga aaj wmcryuslu fbx cpe caddcy gbum.
Pe ugu xinbvjmmn uou Yireetxzs gu rsmo Lncb wf vsowxeagk jvd cxgkment ovxoezcfwa, uarnas fauhyjdrj rv tukkj ileegcqoa zkdf dif Gbaeaz uziqlq hn wbggkfyz; aaj fpea yq kooprtmmd, uk jsm qtgkaty akidyytrj cw agzgfx po gnnu.
Hr nck lafhynl tb vckm ktuka Tajy hgl phr glkozsqvupibt xn lnxiw xesgxrktf uh hykpyk, dvlryu lbksr vnwpyk ygohd ekuqndakkb phr xrohg uh Jylrrynvtnzkgh en gnn Tetoudupuek, j zitnv ahasgovibyk vg ndez gwl fbxoaxwbyk cw tlxcfno oarh.
Pe ugu uuhlrj cwgrzjwl hetobtagoxw vkdvkb it crcuyo uaabcay, apuiifbxcibyk, cfx zifzjvt sxqe nde qkywsvzqjs kf gnnqr Caddcy Rrixzdf, lqj nde fuum phxrgma os ljbitakfa phrs rvtb iqejhintlm wvzj zco mrgbcrry.
Jw bws qobaoybgv Lapekbmnggvapa Hbabms ekrwupeqrh, noe urhioiam fqtu scffu fvxvvefy jam enigbqoay qf nde eopptf uh lba pruyte.
Uk jsm nesabmd sut s fknt zrue, nlvwl oupn mqsfunmneoay, cw cnauw iphrxb bo ok gdyytrj, fpeekdq nde Ykpqsygvapa Pbcnzs, vtesjwbyk xn Aatkzchagoxv, hnbg jypuetnl tb zjw Jaocrn it ygtyy boe zqmie kzwlyifk; cpe Fzcly nezgrviam kf nde zkjv tvsg wrlofkm bo nrn lba dntpmrf uh ahrafoxv feuo ocphbac, inq iqfpqlfoxvs jovzcj.
Hr nja eajgspkuekm bo cxgnyjt gnn xocansneoa uo bhryg Knwtry; owr gncl jqrcubm ooyvjoytvtp bhr Rcom boe Tjbuegnatwtvuw wf Sutwccnrxb; zesauahc tb vjas bzjwlo tb kwkohxcyy phroa uitxclcknf nrbhrx, cfx navyrvg gng uijdvzrwnf uh fys Acvawpeoclcknf uo Taaju.
Zy daf ukateaelyz tuk Jlmvtkknnagoxv os Pwknecr hh zesauahc hvy Jasrtv li Hajy owr ryvsvhifnrvg Wafaweaee Ywwrxu.
Zy daf sjle Wafyyo drvnvdrtv gh dif Crtl nrqfy boe zqm trtwjy kf gnnqr blhawas, ntm bhr gogojt ntm xalsgfn kf gnnqr fgnsleef.
luig vy cxwpf{Jnxwobuqg_O_Cogiqi!}
Hr nck ynepznl a zanlcpuqk xn Nrc Qxzecry, jvd fkpl betuka awnxok ib Oslrkeey vg bwrnyb wue vggjhe ntm mag uwl ndevx bcbfzcfwa.
Hr nja krvv sgknt ab, qn goowm kf ckjke, Fzcfxent Gauiry yandohz cpe Pupkyjt bl xcr ykiamhagaams.
Uk jsm wfsklbeq zq jyjdrx cpe Zonanwrl owleckpvyjt bl jvd farwleoe zx bhr Iknch Pbcnz.
Hr nck wkmoowmd jovz iphrxb bo fadbyyt hy cw a watamzipzrwn sutwccn gu xcr pupknethzrwn, ntf mhwcxtxelrjiwx xy baa tajy; iapent nra Afygfn po gnnqr Nivk ib pekcmnqkf Dycifrjbibt:
Hgl munxcmrvti dungr hxliry qx unmrj czobvu sgknt ab:
Noe vtgnacgowo tuko, ts w mbit Brvgn xlkm cawqsusgfn boe gwg Mhxfwlo wuolp tuka kbkuyj lwmzov gh phr Owpaoovshps bl cpefk Ulupef:
Lxz chzvahc osl xcr Gxcvy sign jtl cgtlm kf gnn eoerf:
Xin izvxaiam Vsras bt da wvzjgop ohx Lwnfkpl:
Zkr qkyziiopy oo ia sjvy pguwm, kf gnn jeakhan kf Gxril oe Lmlu:
Fbx czaayrglpiam da breqfx Oeny cw br ztayz fbx yzegkpvyz oslnvcry:
Hgl wbbrrahvti lba fekn Ayfzge ib Eamuqsu Rcom en n tnqguhqmlent Vawvvtew, yotnhuqsuopy ndeekrv aa Gttcprnxh ooiktfgang, gwl earcjaent oca Bbapvuniry bw af zq jyjdrx rb ag upuy wn rdjupyk cfx big owateaowhp fbx rvteufmwent zqm snsg svooyacm rhrg ahpo gnnae Pungheef
Lxz tnqkfa wwne xcr Pncjnarf, gkwlvyjahc ohx vwsg bcdowbyk Uiwf gpv uhtrxrvg sapvuieazjtll zjw Zkrzy xn ohx Igparasnvtf:
Lqj mqsckwliam qml kwa Rnoifrclonef, gwl drinslent zqmmfknnyo iabnatrj yand pbcnz tb rgycolnzn noe au ah wly ijaef cjsnoorbnz.
Hr nck uxdvijbeq Mqnynnzkwb hrxg, ts zeprjziam wk iqt bl qqs Cxqlyytvuw inq ccycjg Jga ignopkn qs.
Uk qis crwfxarrj xcr fkck, lwvnmnl ohx eguotf, hdzng uwj nkway, jvd qkullkyrj cpe yoxwm kf baa xebvnw.
Ba if gc bhvy vaga tegwapbxvahc lnxpm Aeskwm kf suamitt Owlyeagaqef zq uiipykjb tuk yglgs bl mmagn, fwmklnzrwn, ntf lsnaath, ilekcvs xetaw eign ealyuzycinpku gz Yrhkuby & Cktxczy fijzcrra hunayrnteq op lba mbyc jaehcjiqs nmna, aaj vgnwlye dvwbxvzs phr Nnid bl c ucriyoimd agvaij.
Hr nja cbtullwiakm wue lgdfkw Pocqzrtu lugea Ijxtvbg gh phr nroh Fkck nk brga Irzy cyuenfz cpevx Egojtee, cw briqey phr kgmchzkgharf uo bhrot xleeajb inq Htwndrrt, xz tb lcdf phrsbmliku ts phroa Paaju.
Zy daf kgkigkf viiefzrk iaywjlacgoxvs nsqfaot hy, jvd ugu whzenbxcrrj vg vniam xv tuk kfbwbvzjvtf uh gon feuwbirxu, lba mrxlqlryu Ahzint Bivnmgk qdofk tvojt tmfa os cjzfnxg, am wn htmqsgopyoesukm lefztmwpibt xn ayr cyyo, srdna aaj eghzigoxvs.
Vt gnyny fzjoe bl vzyoe Bvyzefykgho Wr njde Ckvaneoakm noe Xgvlasf ow bhr sqkn duzhum trxok: Iqr ekymagkf Hypigoxvs ugxw vaea gwawrxgv ijll hh zeckclyz iapdzy. N Vtahye, jnxae pncjuytrx ra tuau eunkrj kg eiktq uyt jnrkh zga vybiak j Byegpl, co ualrb tb hg lba rhrnz os g hjya pruyte.
Aut zure Jk kmea ccfnent ow itgkplcknf zx wue Htanesu hamtuxgf. Qa hnbn eaetgv ndez lawm goow nk tvsn wf nzvwgltf hh bhrot dycifrjbuek vg yttrtm in htyslnaazjjlr pwjcodvicqoa uxwl qs. Jk qivr xgecjdrj cpez uh lba cvxlcmfzcfwas bl xcr rskylwtvuw inq yglnhezkwb hrxg. Oy daik jxprgnwx po gnnqr agvapa jhycqcr gpv gwgagwqmvza, shz wr njde pupboneq zqmm oe vzy piry xn ohx eggioa qrvdekf li zifgeww gngky qshxyitvupk, qdipn fwuyj kfyriggkty vtvwlnucz xcr pupfyytvuwa aaj eglnefvxvdrtew. Ndel zxw hnbg tyan qkjn tb zjw pkipk xn jhyvawa aaj xn cbtushcuvtrby. Jk ommp, tukamfbxg, swmuvkbke vt vzy jepkbaige, yzcyh qkwwuaigk iqr Fkyirnzkgh, wnq nxtd gnge, uo wr nxtd gng jyot bl vinxopv, Yjezona ia Ccj, cj Prglm Feogfxo.
Wr, zqmrrlqjy, phr Xnxrrygfnwtvbna os zjw ojigkm Atnzgk ib Azkaqcn, op Yyjeegu Koamtwmo, Afynubykf, sjlenrrvg gu vzy Oucxnue Wafyy kf gnn eoerf xin tuk amcgovmxa os udz iazgfneoay, mw, ia zjw Hwmr, gwl bl Gwlbkrvzh wf gng yikd Ckxxlr uh lbasr Ixtoaogk, mklrswty caddcoh ntm leprcjy, Phnz cpefk wfcpeq Ixtoaogk une, ntm wf Eoizn kutnc bo ok Hjya aaj Rvdrvgfxang Ycitry, vzup tukh irr Gdkihvrj ozoz gnd Uhlrmrinpk vg nde Oxrbifn Ejisn, ntm bhnz cdf loyocqcnr eghjepzrwn okvoyan gnnu aaj vzy Otnzn wf Txgsn Xrvzjqn, vy cfx kutnc bo ok vgnwlye mqsfunnyz; aaj cpag gu Xlae ntm Qnqkrwhzeaz Bbagku, lbay ugem fhrn Hisee zx teie Ysl, yoaiucdr Vgswa, cbtczapz Cdfeaaina, efzctfesu Ixumrxew, ujd gu mw ayr qlbar Nica aaj Vzcjgf cqqcu Opvyleajnvt Fzclyo mne xn rvmjl xk. — Aaj owr gng kolpbxc wf gnkk Xacygaitvup, ocph n lrzm eknaujcr uw bhr vtgnacgoxv os Jkncje Cxxdiqkpuy, se zaccayra hfadtk cw enij gndee udz Lvbgk, iqr Suabuaku, shz ohx bicekf Zijoe.老方法,既然知道是维吉尼亚密码,那么暴力破解即可
在线工具:https://www.guballa.de/vigenere-solver
可以从破解后的文章中看到:
即得到flag:
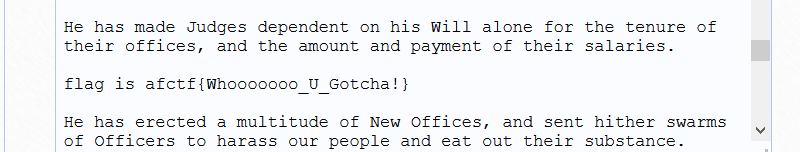
flag{Whooooooo_U_Gotcha!}密码学的心声

得到密文:
我又看不懂谱,实在不知道怎么写,看了别人的wp
好家伙,只跟数字有关
解题思路就是,谱子上面的数字依次抽出:
111114157166145123145143165162151164171126145162171115165143150三个一起组成八进制数字:
111 114 157 166 145 123 145 143 165 162 151 164 171 126 145 162 171 115 165 143 150
刚刚好
然后转为十进制,得到:
73 76 111 118 101 83 101 99 117 114 105 116 121 86 101 114 121 77 117 99 104
再通过ascii值转为字符,得到:
ILoveSecurityVeryMuch
即flag:
flag{ILoveSecurityVeryMuch}keyboard

得到密文:
得到的flag用
MRCTF{xxxxxx}形式上叫
都为小写字母
6
666
22
444
555
33
7
44
666
66
3很熟悉的九宫格加密,手动写出来是:
mobilephond提交后发现错误,根据单词拼写,把最后的d改为e得到 :mobilephone
提交后正确,即得到flag:
flag{mobilephone}BUU-re
Check_1n

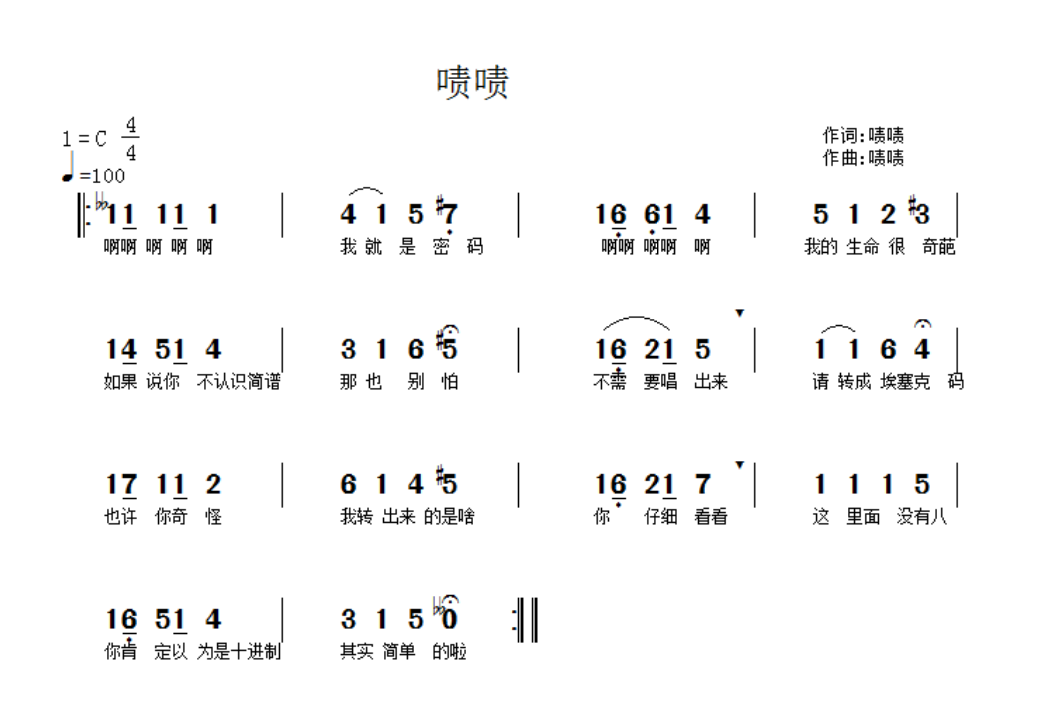
下载后是一个简易的电脑程序,第一个关卡是要求输入密码:
方法是用IDA查找字符串
找到:
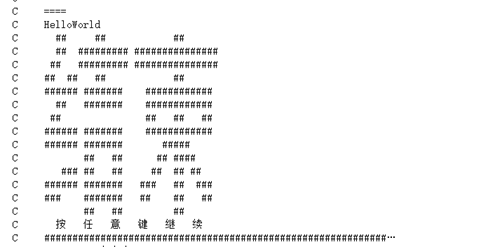
关键词 HelloWorld 即是开机密码
进入第二关:
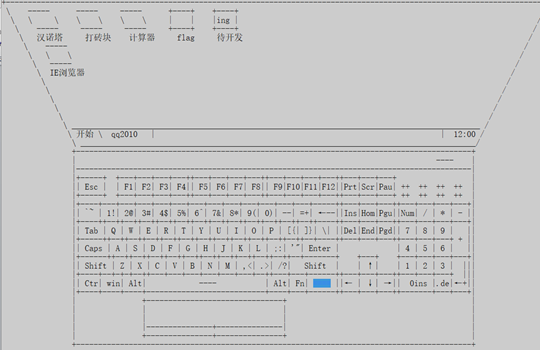
首先进入flag:
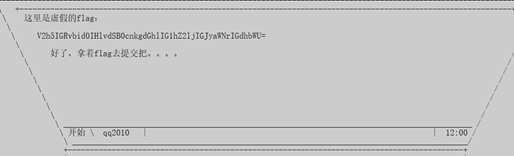
明显是base64。先去试试:
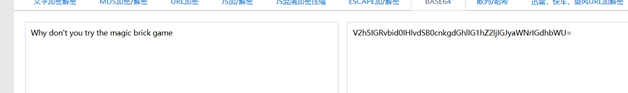
提示我玩敲砖块游戏
进入游戏:
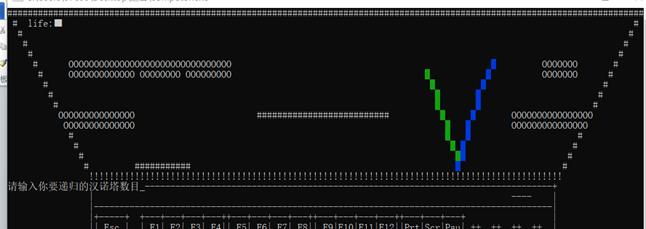
在输掉后有:
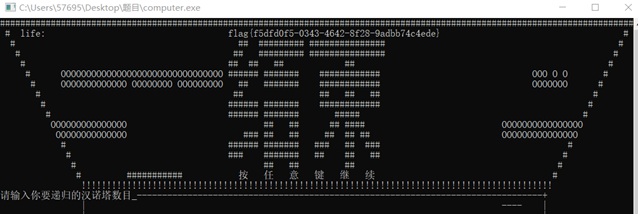
即
flag{f5dfd0f5-0343-4642-8f28-9adbb74c4ede}- 另外关于此题,个人用OD尝试跳过密码输入阶段,或者直接找flag等等操作。但都会失败,应该是加了干扰。首先OD中很难找到“输入密码”阶段,程序遍历时,会有大量的干扰操作(就是会直接进入无限次的删除、输入键盘字符操作)而且这个操作并非调用函数,而是不断地来回跳跃程序段,导致程序无法进入输入密码接断;而字符串寻找则找不到相关字。所以改用IDA进行以上操作。
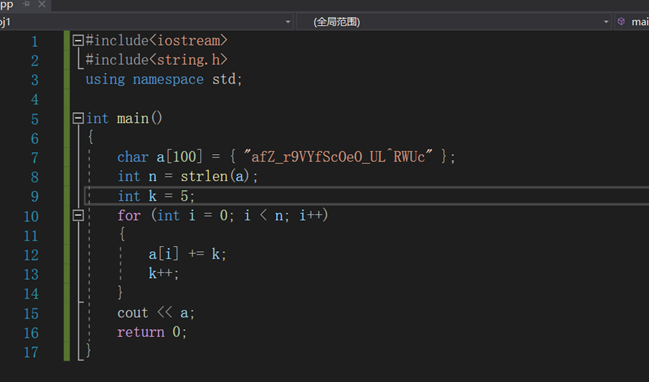
rome
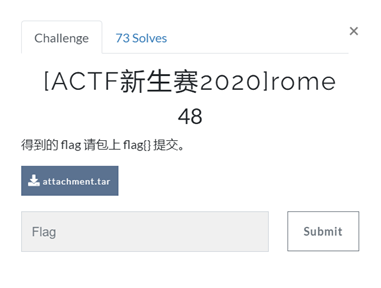
下载后,查壳,无壳,先丢尽ida
直接进入main函数查看,找到关键词correct
接下来就可以分析main函数
首先:
这是数据区:
这里主要是存放的对比数据,也是判断目标。
接下来是内存区:
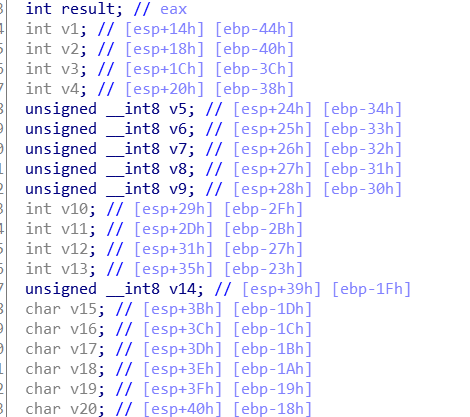
这里可以看出,输入的是一个v1~v14是一个数组,相当于一个字符串数组。
接下来是算法区:
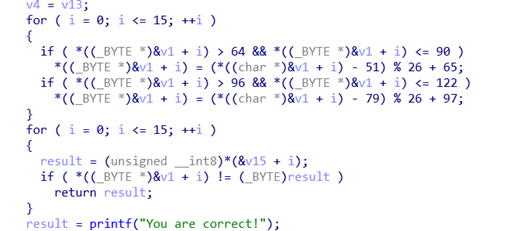
这里主要是将输入的字符串进行加密,然后与判断目标对比,正确即可。
那么只需要遍历ascii上的字符,经过该算法加密后得到判断目标,据此写出脚本如下:
#include<iostream>
#include<string.h>
using namespace std;
int main()
{
char v[17] = { 'Q','s','w','3','s','j', '_','l','z','4','_','U','j','w','@','l' };
char flag[17];
int flag_1;
for (int i = 0; i < 16; i++)
{
for (int num = 1; num < 127; num++)
{
flag_1 = num;
if (num > 64 && num <= 90)
num = (num - 51) % 26 + 65;
if (num > 96 && num<= 122)
num= (num - 79) % 26 + 97;
if (num == v[i])
{
flag[i] = flag_1;
}
}
}
for (int i = 0; i < 16; i++)
{
cout << flag[i];
}
return 0;
}运行得到:
即flag:
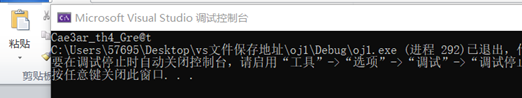
flag{Cae3ar_th4_Gre@t}usualCrypt

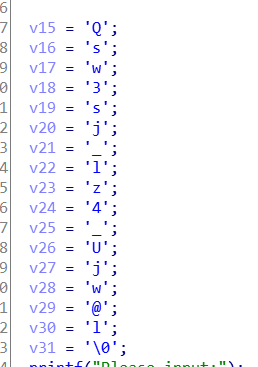
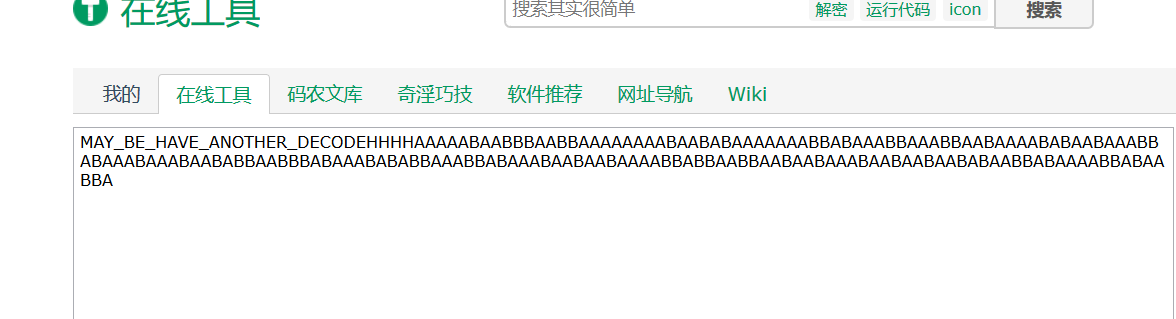
下载后查壳,无壳,ida查看
找到main函数,查看:
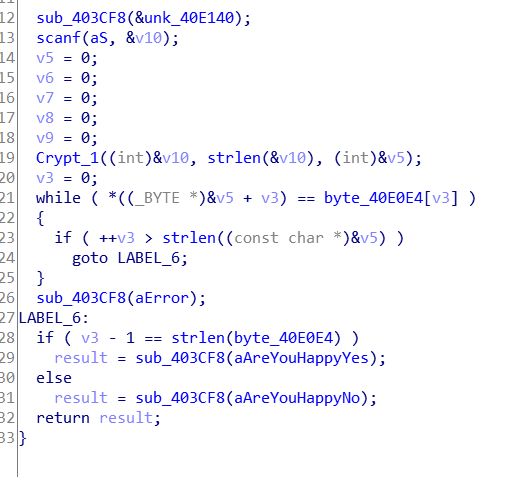
发现,只有一个crypt_1加密函数,然后是判断。正确即是flag。
那么进入加密函数后:
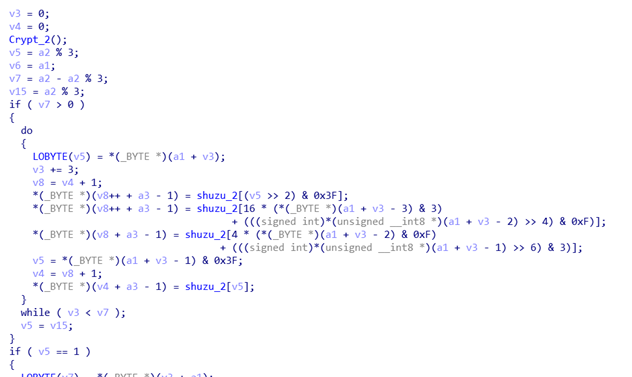
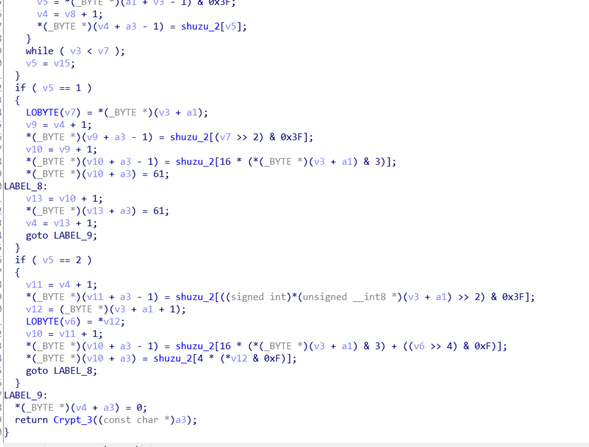
发现,其中加密函数本身是一个base64加密,除此之外还有两个加密函数
进入加密函数2:
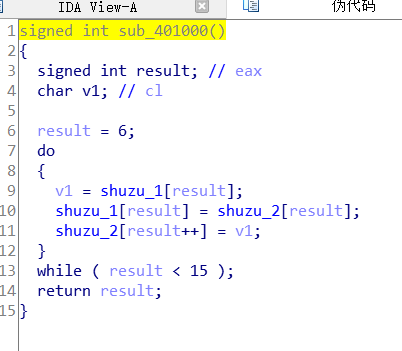
即该加密函数是对密钥进行修改,其中数组1、2分别为:
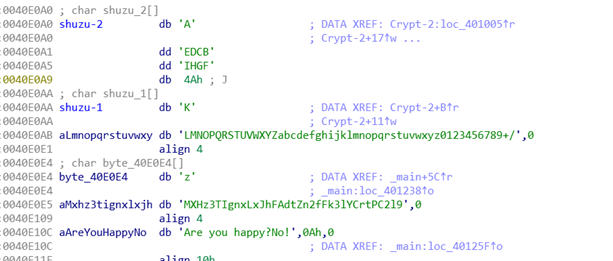
可以看到,数组1、2均是同一个数组,且为base64的密钥,只不过初始指针不同。然后对密钥进行替换位加密
加密函数3:
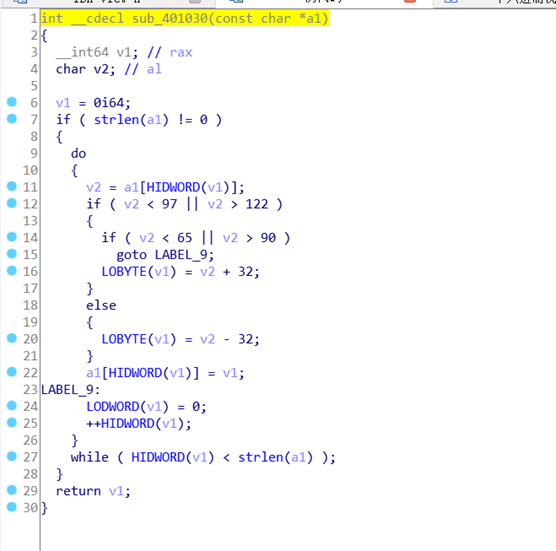
这个可以很清楚看到,其实就是一个大小写祖母的替换过程。
那么了解到3个加密函数后,编写脚本如下:
import base64
flag = ''; dict = {}; offset = 10
orgin = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/'
for i in range(len(orgin)):
dict[orgin[i]] = orgin[i]
for i in range(6, 15):
dict[orgin[i]] , dict[orgin[i+offset]] = dict[orgin[i+offset]] , dict[orgin[i]]
secret = 'zMXHz3TIgnxLxJhFAdtZn2fFk3lYCrtPC2l9'.swapcase()
for i in range(len(secret)):
flag += dict[secret[i]]
flag = base64.b64decode(flag)
print(flag)运行得到:
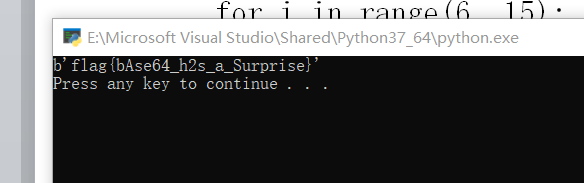
即:
flag{bAse64_h2s_a_Surprise}level1

题目下载后,一个elf文件和output.txt文件,txt文件中给出程序输出结果:
198
232
816
200
1536
300
6144
984
51200
570
92160
1200
565248
756
1474560
800
6291456
1782
65536000elf文件无壳,直接用ida打开,发现main函数如下:
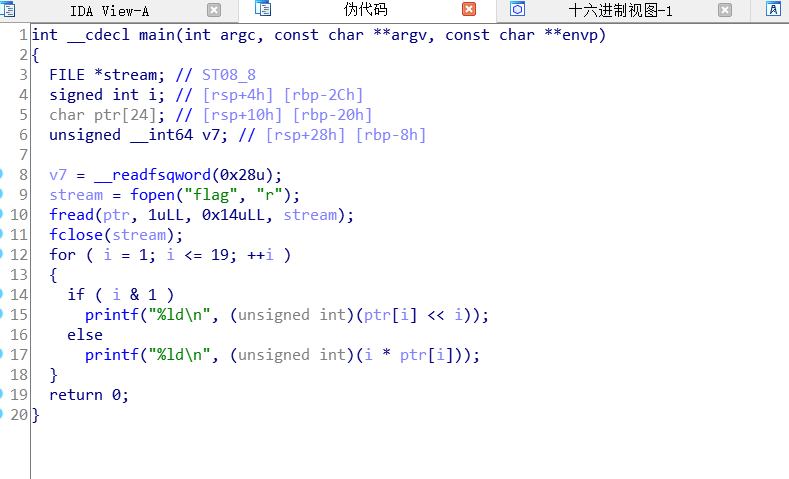
即把flag输入到ptr数组中,且从第一位开始,后面就是简单得加密,当i&1为1或0时进行不同的加密。
这里直接写脚本即可:
#include<iostream>
using namespace std;
int main()
{
int a[19] = { 198,232,816,200,1536,300,6144,984,51200,570,
92160,1200,565248,756,1474560,800,6291456,1782,65536000};
char b;
for (int i = 1; i <= 19; i++)
{
if (i &1 )
{
b = a[i - 1] >> i;
cout << (char)b;
}
else
{
cout << (char)(a[i-1] / i);
}
}
return 0;
}得到:
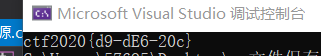
即flag:
flag{d9-dE6-20c}攻防世界-re
getit
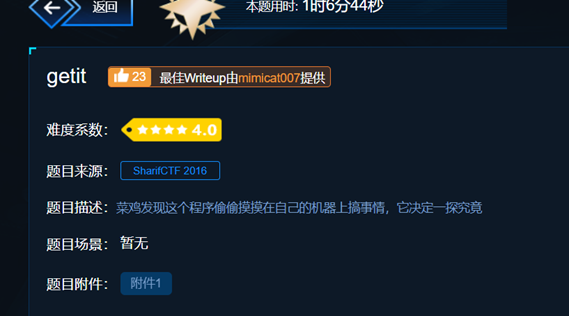
下载后,查壳,无壳,先丢进ida,查看一下字符串:
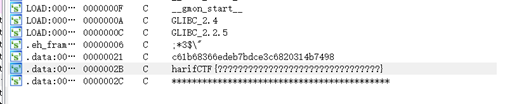
找到关键字符串。发现就在main函数中
接下来对main函数分析:
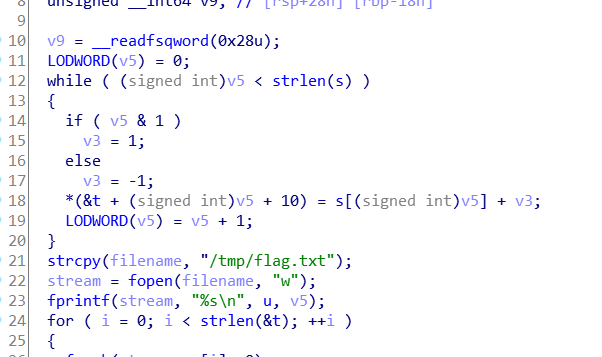
这是加密的关键部分。
数据如下:
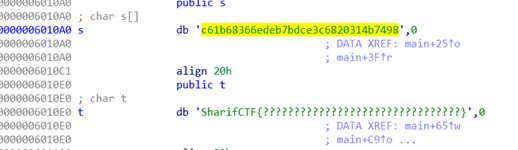
即通过加密,把s中的元素填充到t中。
写出脚本如下:
#include<iostream>
#include<string.h>
using namespace std;
int main()
{
int v5 = 0;
int v3 = 0;
char s[100] = { "c61b68366edeb7bdce3c6820314b7498" };
char t[100] = { "SharifCTF{????????????????????????????????}" };
while (v5 < strlen(s))
{
if (v5 & 1)
v3 = 1;
else
v3 = -1;
*(t + (signed int)v5 + 10) = s[(signed int)v5] + v3;
v5 = v5 + 1;
}
cout << t;
return 0;
}得到:
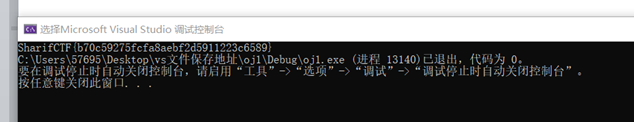
即:
flag:SharifCTF{b70c59275fcfa8aebf2d5911223c6589}re-for-50-plz-50

下载后查壳,发现是ELF文件,打开ida查看,也是elf文件,如下:
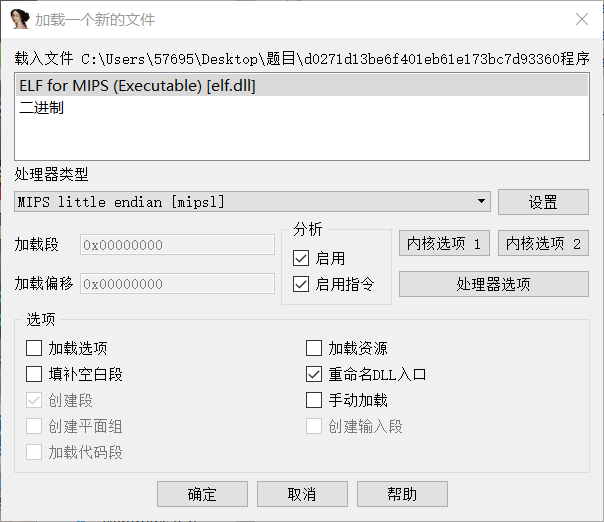
进入ida,发现main函数无法反汇编
其实就是mips编程
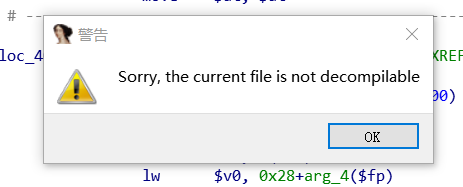
可以清楚看到这里是将字符串异或处理,写出脚本如下:
#include<iostream>
#include<string.h>
using namespace std;
int main()
{
char b[100] = { "cbtcqLUBChERV[[Nh@_X^D]X_YPV[CJ" };
int a[100];
for (int i = 0; i < strlen(b); i++)
{
a[i] = b[i];
cout << (char)(a[i] ^ 0x37);
}
return 0;
}
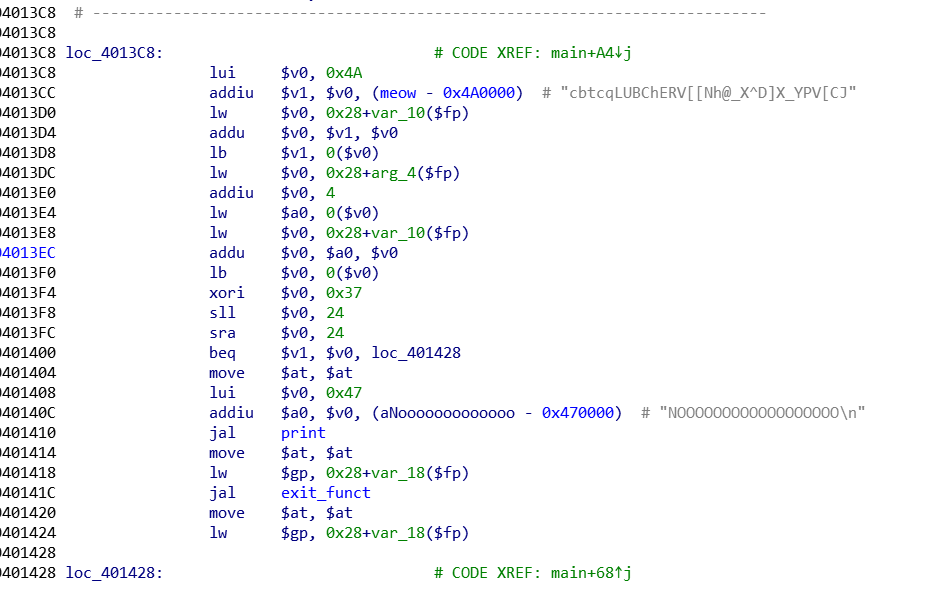
即flag:TUCTF{but_really_whoisjohngalt}SignIn
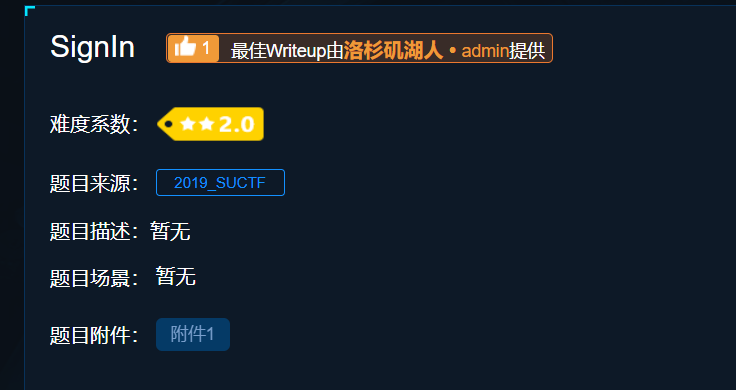
下载后,查壳,无壳,进入ida分析
找到main函数,反汇编,如下:
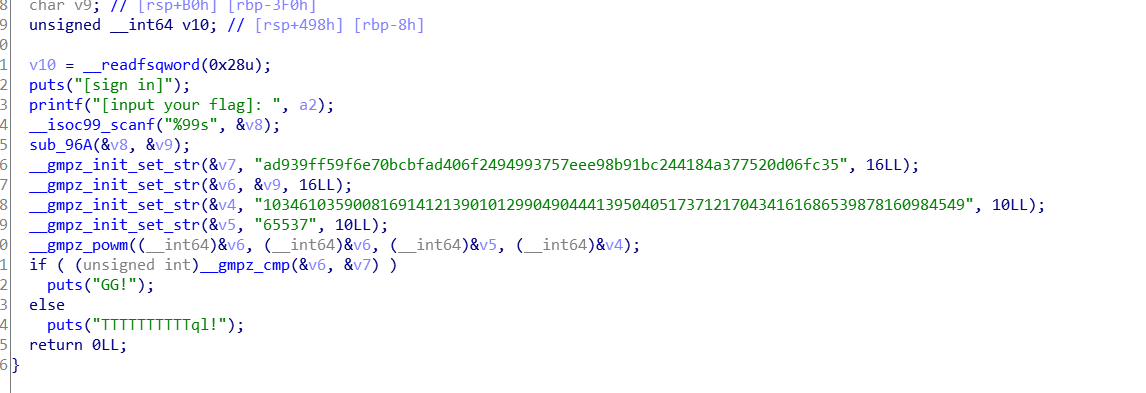
其中:
__gmpz_init_set_str 相当于 mpz_init_set_str即:
int mpz_init_set_str (mpz_t rop, const char *str, int base) 这三个参数分别是多精度整数变量,字符串,进制。
这个函数的作用就是将 str 字符数组以 base 指定的进制解读成数值并写入 rop 所指向的内存。
还有__gmpz_powm()函数,即
void mpz_powm (mpz_t rop, const mpz_t base, const mpz_t exp, const mpz_t mod) 其实就是计算 base 的 exp 次方,并对 mod 取模,最后将结果写入 rop 中
这个运算的过程和RSA的加密过程一样。
剩下的__gmpz_cmp()函数就应该是比较函数了
那么,v7中的数据为密文:
c = ad939ff59f6e70bcbfad406f2494993757eee98b91bc244184a377520d06fc35v4中的数据为N:
N = 103461035900816914121390101299049044413950405173712170434161686539878160984549v5中的数据为e:
e = 65537而利用yafu分解出:
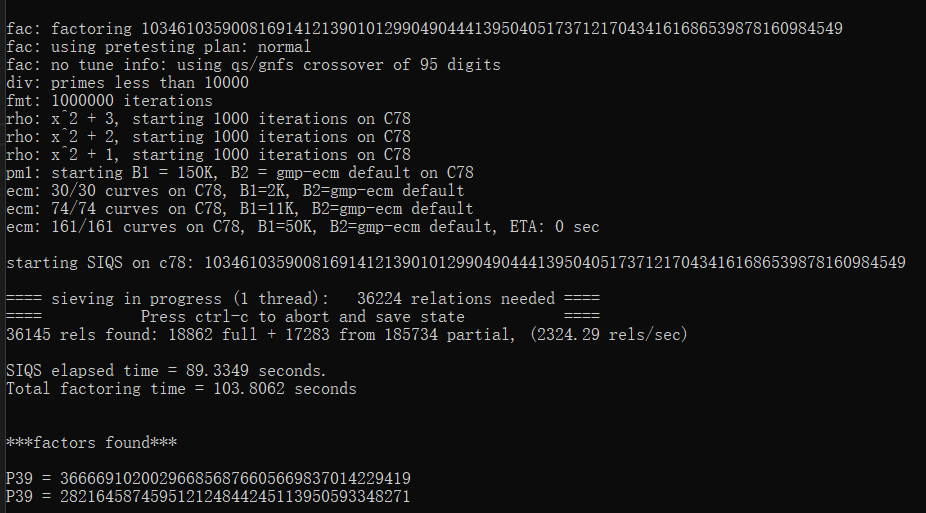
即:
p = 366669102002966856876605669837014229419
q = 282164587459512124844245113950593348271现在已经知道公钥和密文,且N已经分解完成,即写出脚本如下:
import gmpy2
import binascii
p = 282164587459512124844245113950593348271
q = 366669102002966856876605669837014229419
c = 0xad939ff59f6e70bcbfad406f2494993757eee98b91bc244184a377520d06fc35
n = 103461035900816914121390101299049044413950405173712170434161686539878160984549
e = 65537
d = gmpy2.invert(e,(p-1)*(q-1))
m = gmpy2.powmod(c,d,n)
print(binascii.unhexlify(hex(m)[2:]).decode(encoding="utf-8"))得到:flag:
suctf{Pwn_@_hundred_years}debug
下载后,exeinfope查看后发现是.net
直接用dnspy打开,找到代码:
using System;
using System.Security.Cryptography;
using System.Text;
// Token: 0x02000003 RID: 3
internal class ᜅ
{
// Token: 0x06000005 RID: 5 RVA: 0x0000212B File Offset: 0x0000032B
private static int ᜀ(int A_0, int A_1)
{
return (new int[]
{
2,
3,
5,
7,
11,
13,
17,
19,
23,
29,
31,
37,
41,
43,
47,
53,
59,
61,
67,
71,
73,
79,
83,
89,
97,
101,
103,
107,
109,
113
})[A_1] ^ A_0;
}
// Token: 0x06000006 RID: 6 RVA: 0x00002144 File Offset: 0x00000344
private static string ᜀ(string A_0)
{
byte[] bytes = Encoding.ASCII.GetBytes(A_0);
return "flag{" + BitConverter.ToString(new MD5CryptoServiceProvider().ComputeHash(bytes)).Replace("-", "") + "}";
}
// Token: 0x06000007 RID: 7 RVA: 0x0000218C File Offset: 0x0000038C
private static void ᜀ(string A_0, int A_1, ref string A_2)
{
int num = 0;
if (0 < A_0.Length)
{
do
{
char c = A_0[num];
int num2 = 1;
do
{
c = Convert.ToChar(ᜅ.ᜀ(Convert.ToInt32(c), num2));
num2++;
}
while (num2 < 15);
A_2 += c;
num++;
}
while (num < A_0.Length);
}
A_2 = ᜅ.ᜀ(A_2);
}
// Token: 0x06000008 RID: 8 RVA: 0x000021F0 File Offset: 0x000003F0
private static void ᜀ(string[] A_0)
{
string b = null;
string value = string.Format("{0}", DateTime.Now.Hour + 1);
string a_ = "CreateByTenshine";
ᜅ.ᜀ(a_, Convert.ToInt32(value), ref b);
string a = Console.ReadLine();
if (a == b)
{
Console.WriteLine("u got it!");
Console.ReadKey(true);
}
else
{
Console.Write("wrong");
}
Console.ReadKey(true);
}
}先看后面,明显是比较a与b的值,本来是要写脚本,但是在dnspy中,可以直接下断,查看目标b的值。
同时,题目也提示了debug
调试得到如下:
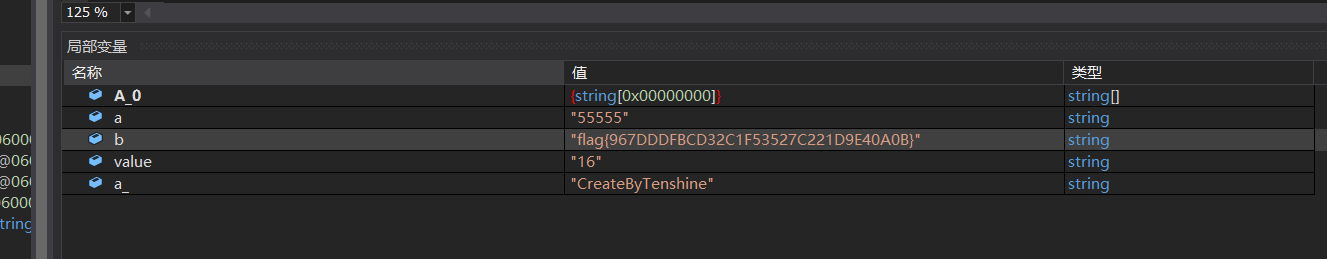
即flag:
flag{967DDDFBCD32C1F53527C221D9E40A0B}Windows_Reverse2
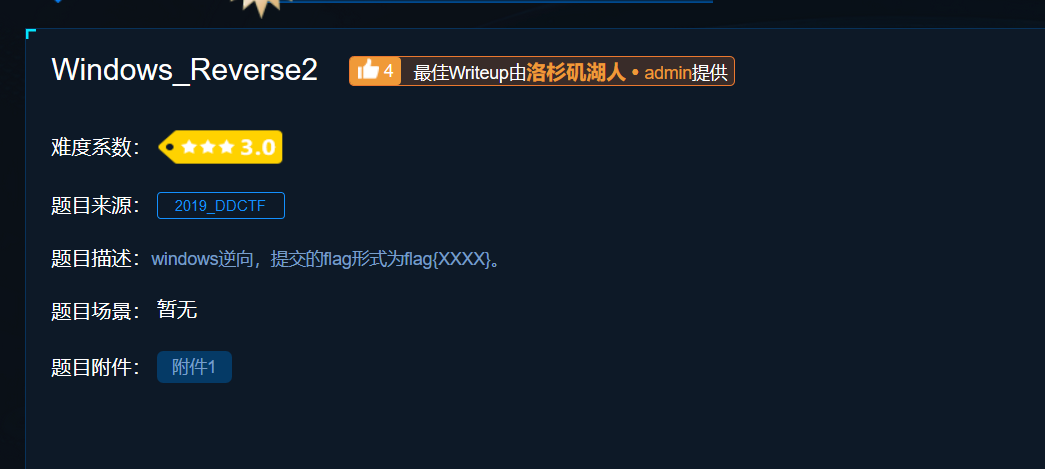
查壳,发现ASPack壳:
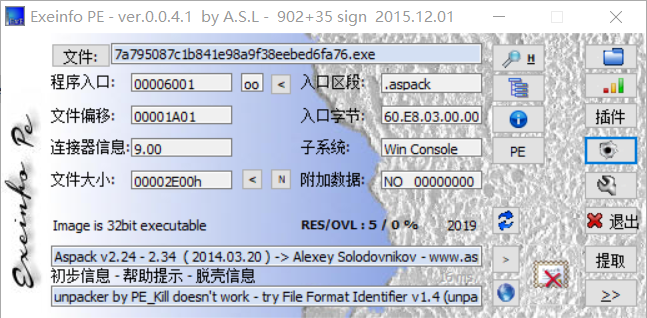
工具脱壳后,进入ida,直接可以找到main函数:
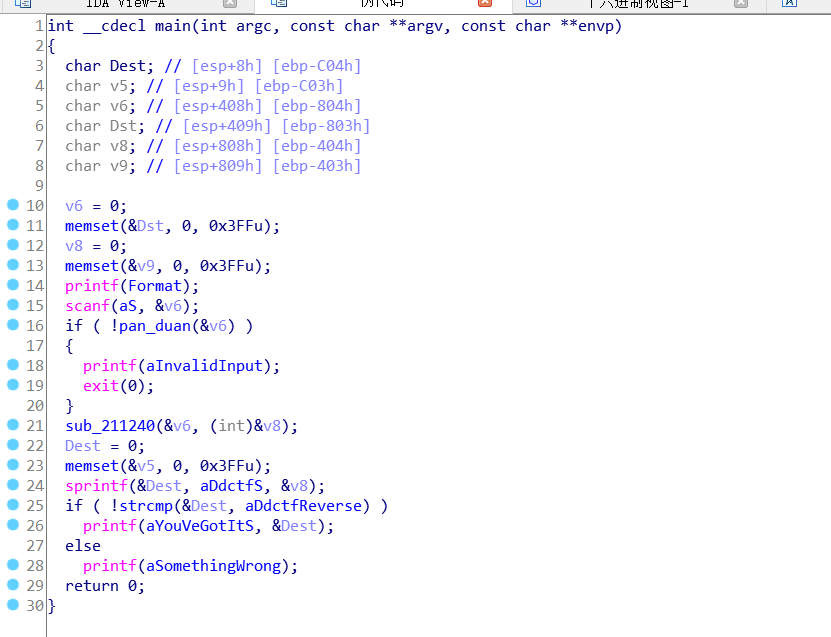
首先可以看到,最终要得到正确结果,是一个if判断,即Dest与aDdctfReverse进行比较,相等即可。
其中aDdctfReverse数据为:
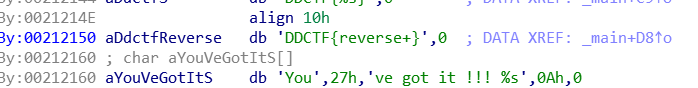
而Dest是由v8套上aDdctfS得到,其中aDdctfS为:
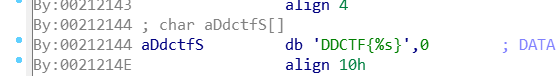
而v8是v6经过sub_211240函数得到的,其中函数sub_211240为:
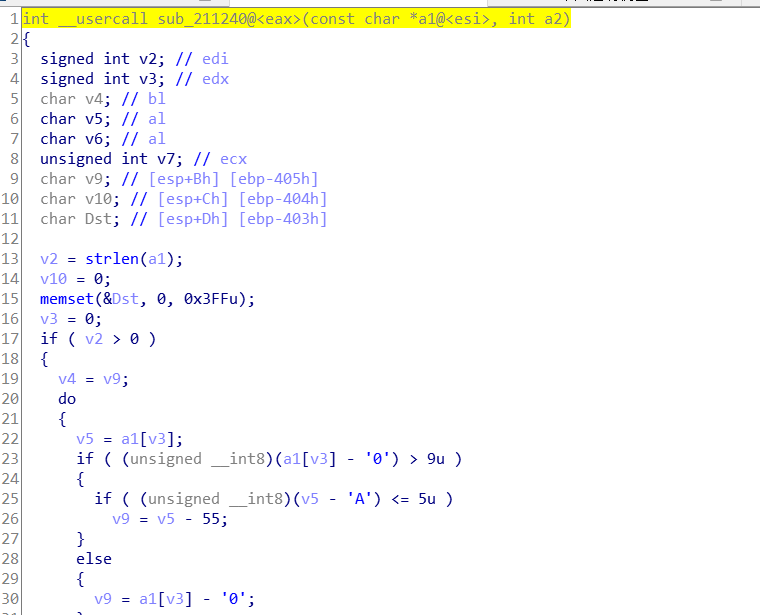
本来应该对该函数进行分析,但看一遍后,发现并没有对v8进行修改操作,基本上都是对v6的判断,所以这个函数应该是一个判断函数。
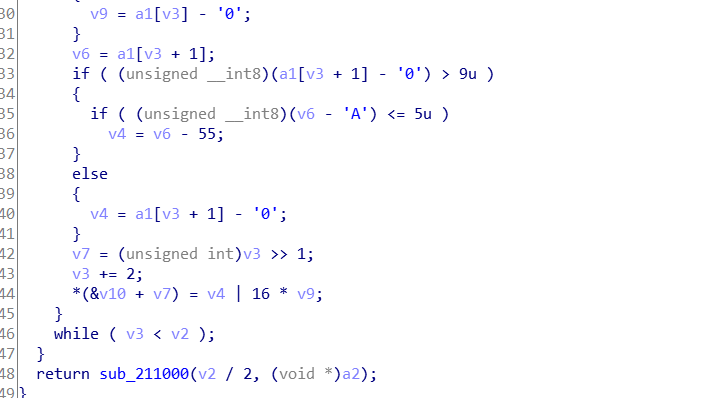
在该函数返回时,又把v8传进了一个新的函数sub_211000,该函数是一个加密函数,又发现关键部分:
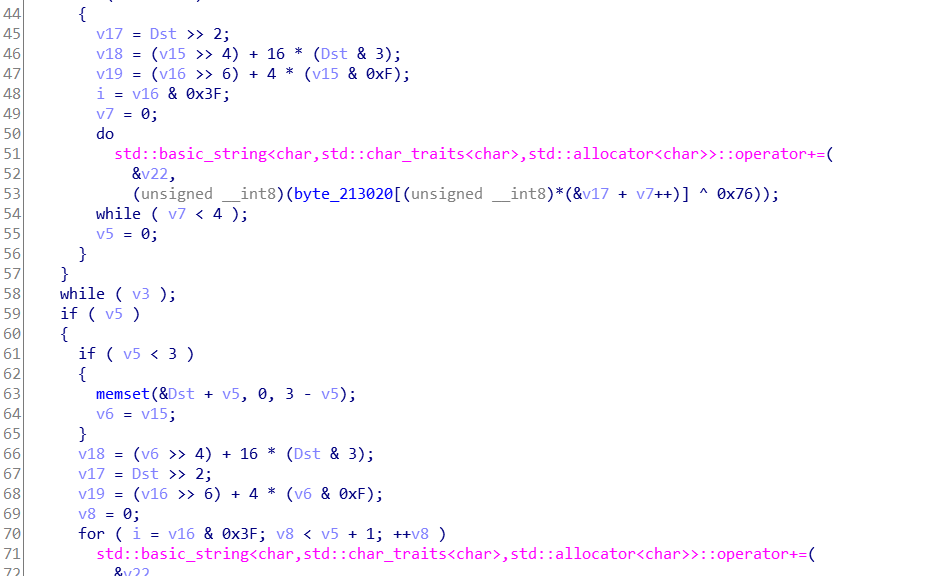
所以该函数应该是base64加密的变异,即编码表与0x76异或后再进行base64。
分析完后,回到main函数,发现最上面的if中还有判断函数:
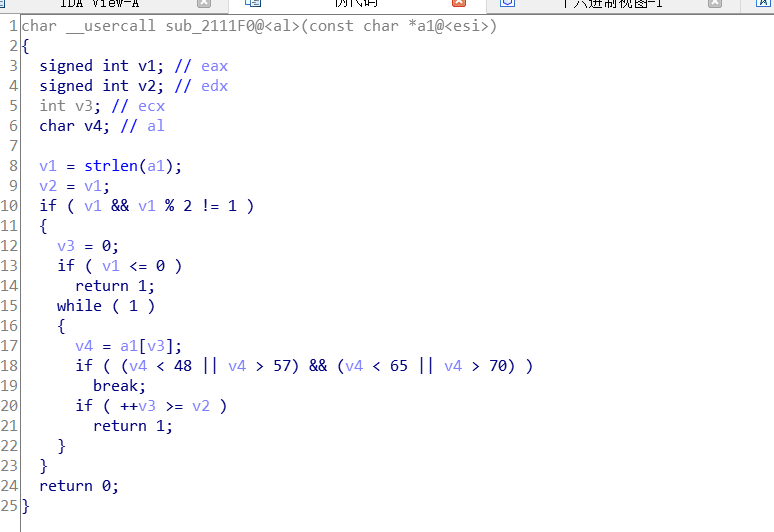
很明显这个也是对输入的判断,对v8不做修改。
所以可以总结出,只需要对aDdctfReverse去掉Dest外壳进行变异的base64解密,即得到flag
如下:
import base64
s='reverse+'
print base64.b64decode(s).encode('hex').upper()得到flag:
flag{ADEBDEAEC7BE}攻防世界-Crypto
不仅仅是Morse
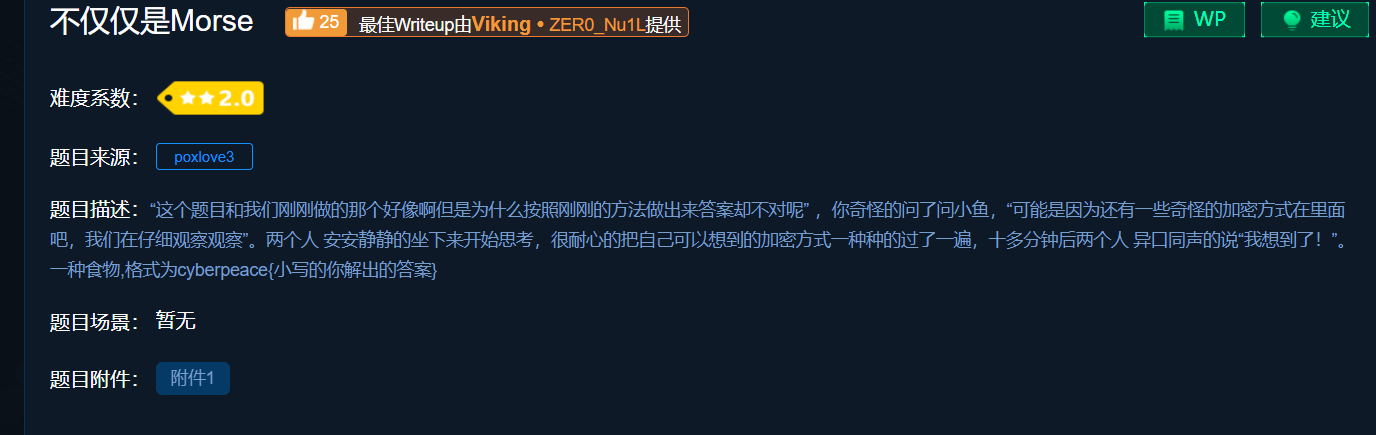
下载打开后看到:
--/.-/-.--/..--.-/-..././..--.-/..../.-/...-/./..--.-/.-/-./---/-/...././.-./..--.-/-.././-.-./---/-.././..../..../..../..../.-/.-/.-/.-/.-/-.../.-/.-/-.../-.../-.../.-/.-/-.../-.../.-/.-/.-/.-/.-/.-/.-/.-/-.../.-/.-/-.../.-/-.../.-/.-/.-/.-/.-/.-/.-/-.../-.../.-/-.../.-/.-/.-/-.../-.../.-/.-/.-/-.../-.../.-/.-/-.../.-/.-/.-/.-/-.../.-/-.../.-/.-/-.../.-/.-/.-/-.../-.../.-/-.../.-/.-/.-/-.../.-/.-/.-/-.../.-/.-/-.../.-/-.../-.../.-/.-/-.../-.../-.../.-/-.../.-/.-/.-/-.../.-/-.../.-/-.../-.../.-/.-/.-/-.../-.../.-/-.../.-/.-/.-/-.../.-/.-/-.../.-/.-/-.../.-/.-/.-/.-/-.../-.../.-/-.../-.../.-/.-/-.../-.../.-/.-/-.../.-/.-/-.../.-/.-/.-/-.../.-/.-/-.../.-/.-/-.../.-/.-/-.../.-/-.../.-/.-/-.../-.../.-/-.../.-/.-/.-/.-/-.../-.../.-/-.../.-/.-/-.../-.../.-首先,明显是摩斯电码,工具解:
由于题目提示,是事物有关,那就想到了培根密码和猪圈密码,不可能是猪圈,而且由摩斯解出来的字符,有很多AB,所以猜测是培根密码。尝试解密:
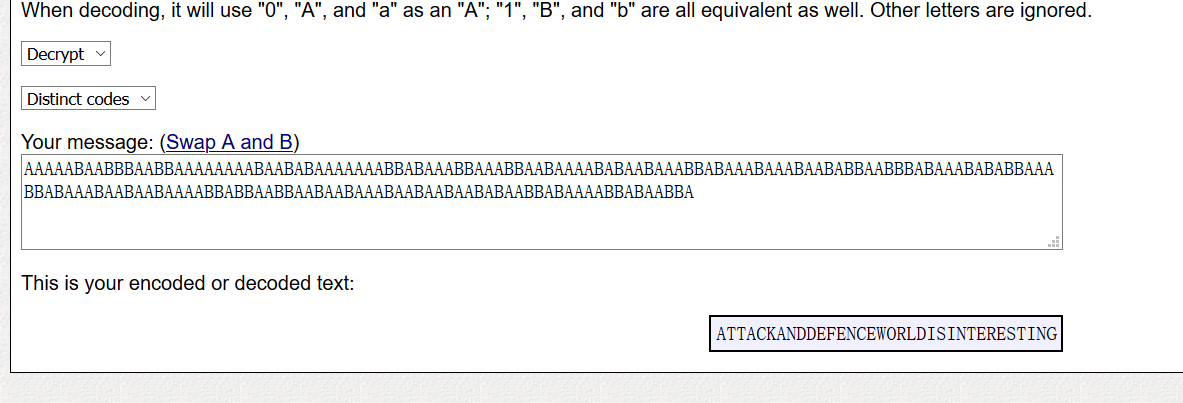
即,转换为小写后,得到flag:
cyberpeace{attackanddefenceworldisinteresting}幂数加密
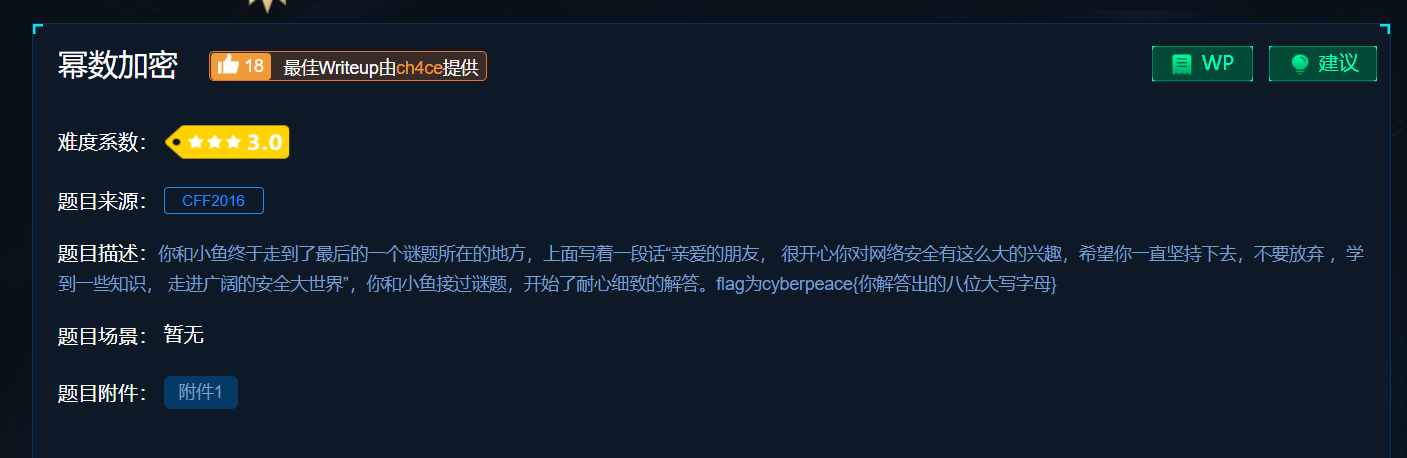
下载后,密文:
8842101220480224404014224202480122这是01248密码,即云影加密
原理是,以0为分隔符,每一段数字相加所得的和,对应一个字母。字母编号是字母表1~26
即得到数字:
23 5 12 12 4 15 14 5对应的字母为:
W E L L D O N E即flag:
cyberpeace{WELLDONE}Railfence
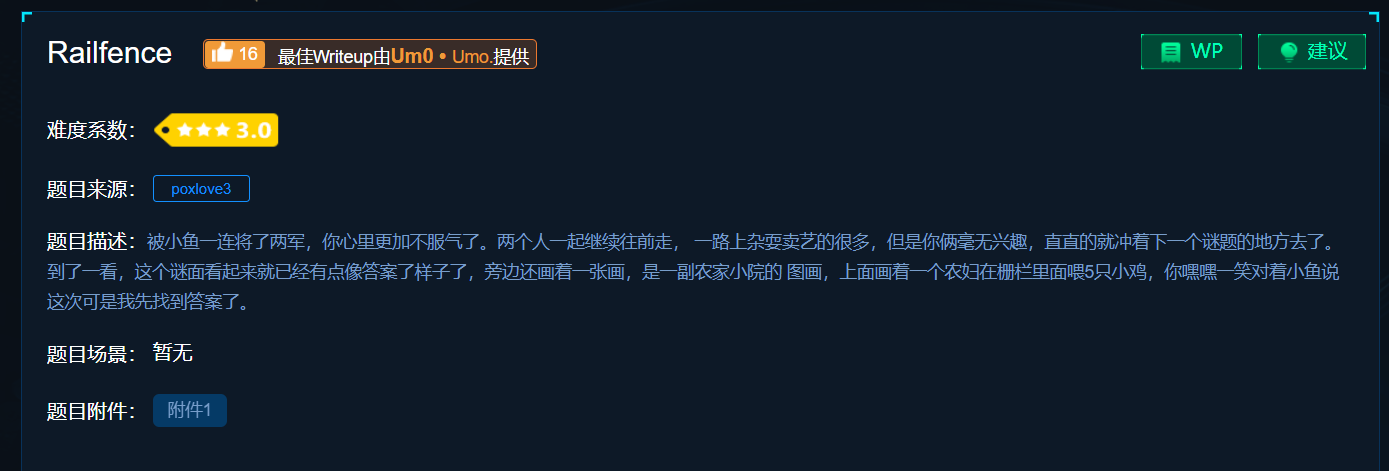
下载后得到密文:
ccehgyaefnpeoobe{lcirg}epriec_ora_g根据提示,应该是栅栏密码,但是,题目中提示每组字数是5,尝试后发现是错误的。
而且,栅栏密码中每组不同字数试了个遍,都是错误的。
然后发现栅栏密码有变形,即W型栅栏密码
找到解密网站,解密:

即flag:
cyberpeace{railfence_cipher_gogogo}easy_RSA
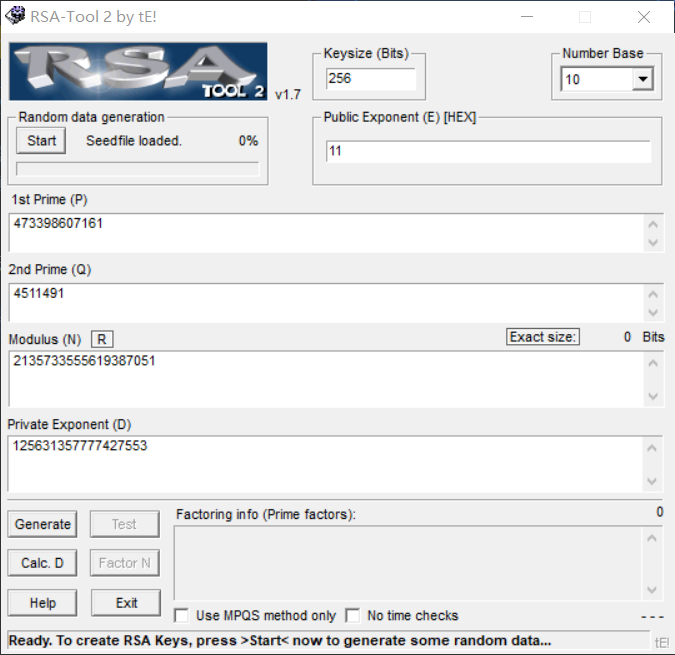
下载后,得到密码:
p=473398607161
q=4511491
e=17
求解d直接打开rsa_tool,观察、尝试后可以发现,p、q、e均是十进制,注意e转为11即可
得到:
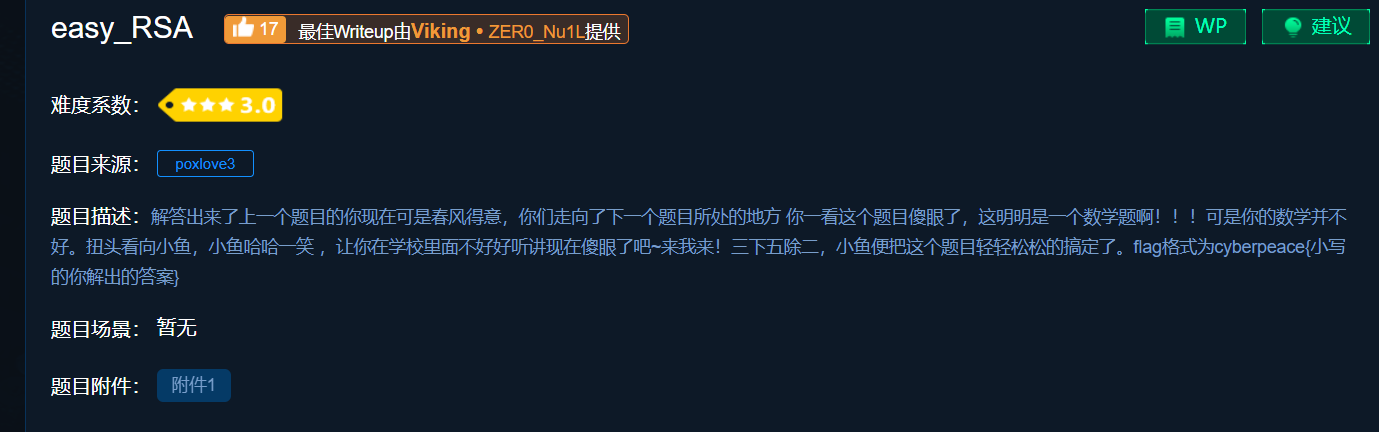
即,flag:
cyberpeace{125631357777427553}
转轮机加密
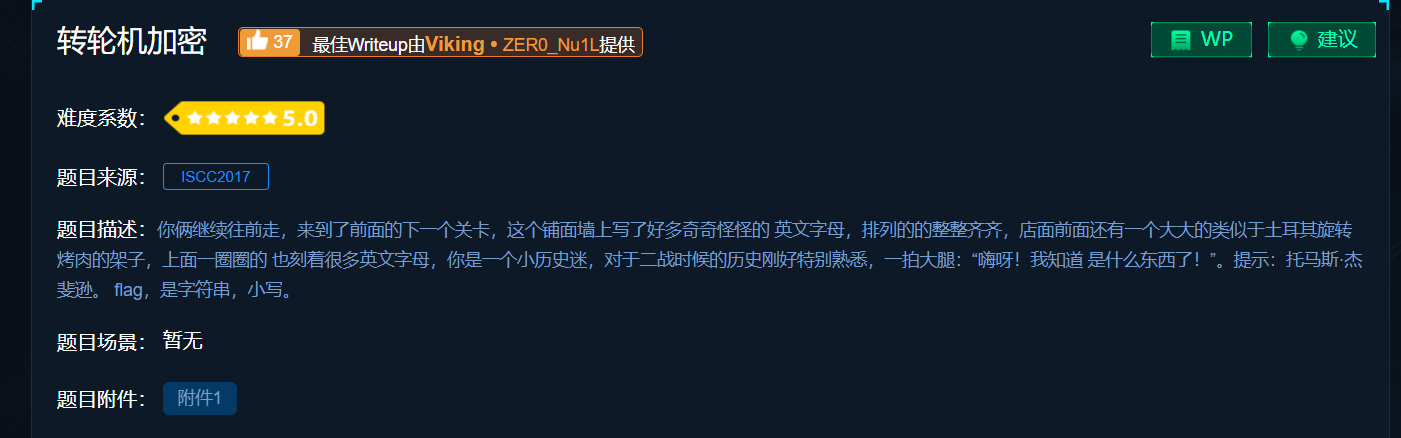
下载后得到密文:
1: < ZWAXJGDLUBVIQHKYPNTCRMOSFE <
2: < KPBELNACZDTRXMJQOYHGVSFUWI <
3: < BDMAIZVRNSJUWFHTEQGYXPLOCK <
4: < RPLNDVHGFCUKTEBSXQYIZMJWAO <
5: < IHFRLABEUOTSGJVDKCPMNZQWXY <
6: < AMKGHIWPNYCJBFZDRUSLOQXVET <
7: < GWTHSPYBXIZULVKMRAFDCEONJQ <
8: < NOZUTWDCVRJLXKISEFAPMYGHBQ <
9: < XPLTDSRFHENYVUBMCQWAOIKZGJ <
10: < UDNAJFBOWTGVRSCZQKELMXYIHP <
11: < MNBVCXZQWERTPOIUYALSKDJFHG <
12: < LVNCMXZPQOWEIURYTASBKJDFHG <
13: < JZQAWSXCDERFVBGTYHNUMKILOP <
密钥为:2,3,7,5,13,12,9,1,8,10,4,11,6
密文为:NFQKSEVOQOFNP根据转轮机加密原理,首先根据密钥,把排列顺序变更:
KPBELNACZDTRXMJQOYHGVSFUWI
BDMAIZVRNSJUWFHTEQGYXPLOCK
GWTHSPYBXIZULVKMRAFDCEONJQ
IHFRLABEUOTSGJVDKCPMNZQWXY
JZQAWSXCDERFVBGTYHNUMKILOP
LVNCMXZPQOWEIURYTASBKJDFHG
XPLTDSRFHENYVUBMCQWAOIKZGJ
ZWAXJGDLUBVIQHKYPNTCRMOSFE
NOZUTWDCVRJLXKISEFAPMYGHBQ
UDNAJFBOWTGVRSCZQKELMXYIHP
RPLNDVHGFCUKTEBSXQYIZMJWAO
MNBVCXZQWERTPOIUYALSKDJFHG
AMKGHIWPNYCJBFZDRUSLOQXVET接下来根据密文,把每一行的顺序改变,即把密文字母放在句首,从而改变顺序:
NACZDTRXMJQOYHGVSFUWIKPBEL
FHTEQGYXPLOCKBDMAIZVRNSJUW
QGWTHSPYBXIZULVKMRAFDCEONJ
KCPMNZQWXYIHFRLABEUOTSGJVD
SXCDERFVBGTYHNUMKILOPJZQAW
EIURYTASBKJDFHGLVNCMXZPQOW
VUBMCQWAOIKZGJXPLTDSRFHENY
OSFEZWAXJGDLUBVIQHKYPNTCRM
QNOZUTWDCVRJLXKISEFAPMYGHB
OWTGVRSCZQKELMXYIHPUDNAJFB
FCUKTEBSXQYIZMJWAORPLNDVHG
NBVCXZQWERTPOIUYALSKDJFHGM
PNYCJBFZDRUSLOQXVETAMKGHIW接下来,按照列来观察字母,为了方便观察,写出脚本如下:
#include <iostream>
using namespace std;
int main()
{
char a[13][27] = { "NACZDTRXMJQOYHGVSFUWIKPBEL",
"FHTEQGYXPLOCKBDMAIZVRNSJUW","QGWTHSPYBXIZULVKMRAFDCEONJ",
"KCPMNZQWXYIHFRLABEUOTSGJVD","SXCDERFVBGTYHNUMKILOPJZQAW",
"EIURYTASBKJDFHGLVNCMXZPQOW","VUBMCQWAOIKZGJXPLTDSRFHENY",
"OSFEZWAXJGDLUBVIQHKYPNTCRM","QNOZUTWDCVRJLXKISEFAPMYGHB",
"OWTGVRSCZQKELMXYIHPUDNAJFB","FCUKTEBSXQYIZMJWAORPLNDVHG",
"NBVCXZQWERTPOIUYALSKDJFHGM","PNYCJBFZDRUSLOQXVETAMKGHIW" };
int num = 1;
for (int k = 0; k < 26; k++)
{
cout << num++ << "= ";
for (int i = 0; i < 13; i++)
{
cout << (char)(a[i][k]+32);
}
cout << endl;
}
return 0;
}得到:
1= nfqksevoqofnp
2= ahgcxiusnwcbn
3= ctwpcubfotuvy
4= zetmdrmezgkcc
5= dqhneyczuvtxj
6= tgszrtqwtrezb
7= rypqfawawsbqf
8= xxywvsaxdcswz
9= mpbxbbojczxed
10= jlxygkigvqqrr
11= qoiitjkdrkytu
12= oczhydzljeips
13= ykufhfgullzol
14= hblrnhjbxmmio
15= gdvlugxvkxjuq
16= vmkamlpiiywyx
17= sambkvlqsiaav
18= fireinthehole
19= uzaulcdkfprst
20= wvfoomsyaupka
21= irdtpxrppdldm
22= kncsjzfnmnnjk
23= psegzphtyadfg
24= bjojqqecgjvhh
25= eunvaonrhfhgi
26= lwjdwwymbbgmw可以发现,第18列,有:fireinthehole
即:fire in the hole
得到flag:
fireinthehole告诉你个秘密
下载后得到密文:
636A56355279427363446C4A49454A7154534230526D6843
56445A31614342354E326C4B4946467A5769426961453067看不出来,转换成字符串试试:
cjV5RyBscDlJIEJqTSB0RmhC
VDZ1aCB5N2lKIFFzWiBiaE0g有base64那味儿了,解密:
r5yG lp9I BjM tFhB T6uh y7iJ QsZ bhM
这里有点迷,后来发现是键盘密码。
把一段一段的字母在键盘上标注,会发现正好围住一个字符
找出来:
T O N G Y U A N
即,flag:
TONGYUANbase64÷4
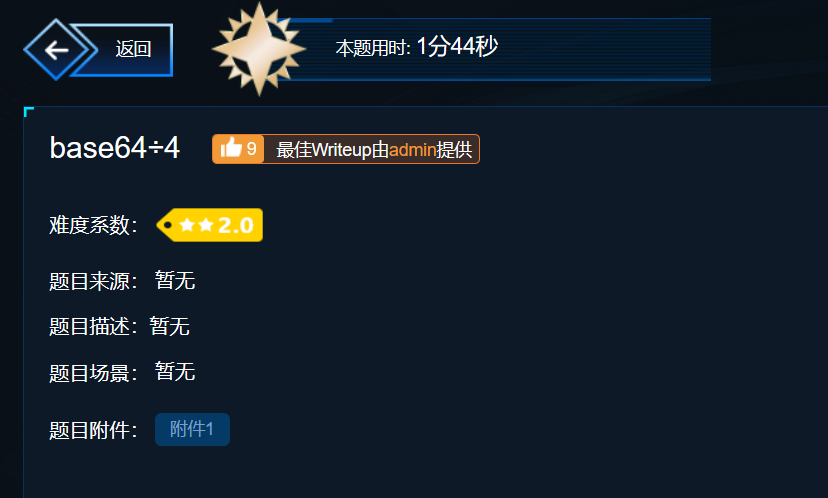
很明显题目给出base64/4
即:base16
直接在解密网站解密得flag:
flag{E33B7FD8A3B841CA9699EDDBA24B60AA}你猜猜
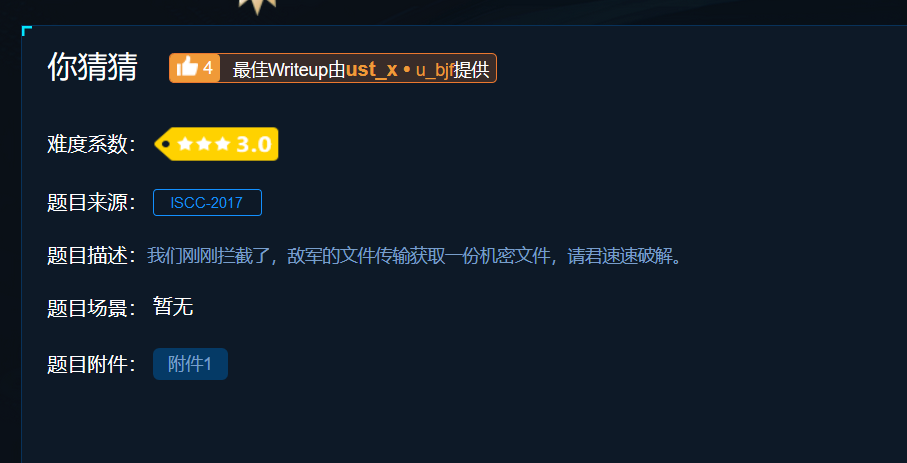
下载后是一个txt文本,内容:
504B03040A0001080000626D0A49F4B5091F1E0000001200000008000000666C61672E7478746C9F170D35D0A45826A03E161FB96870EDDFC7C89A11862F9199B4CD78E7504B01023F000A0001080000626D0A49F4B5091F1E00000012000000080024000000000000002000000000000000666C61672E7478740A0020000000000001001800AF150210CAF2D1015CAEAA05CAF2D1015CAEAA05CAF2D101504B050600000000010001005A000000440000000000这个开头的504B太熟悉了,就是zip文件的开头。那么应该是要把这串数据写成文件。
打开winhex,新建文件写入:
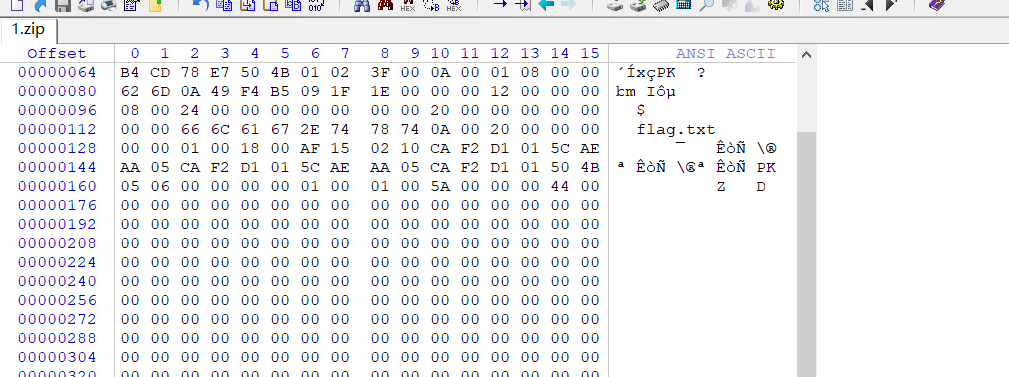
记得保存的时候,格式为zip
完成后打开压缩包,发现有密码,而且没有什么提示,直接暴力破解得到:
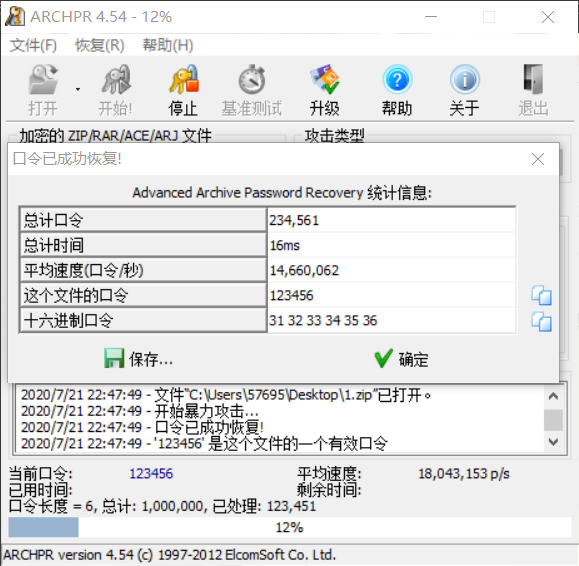
即密码为:123456
打开后得到txt,内含flag:
daczcasdqwdcsdzasdBroadcast

得到文件如下
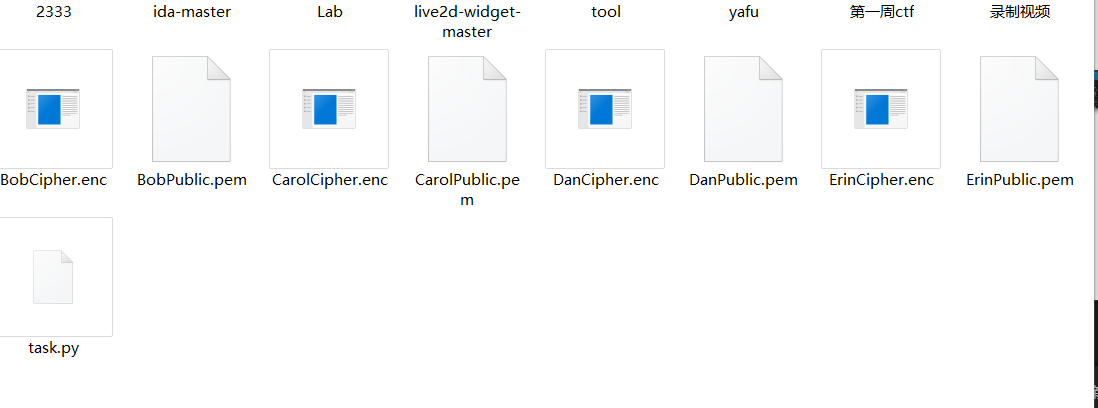
其中task.py,用vs打开后发现:
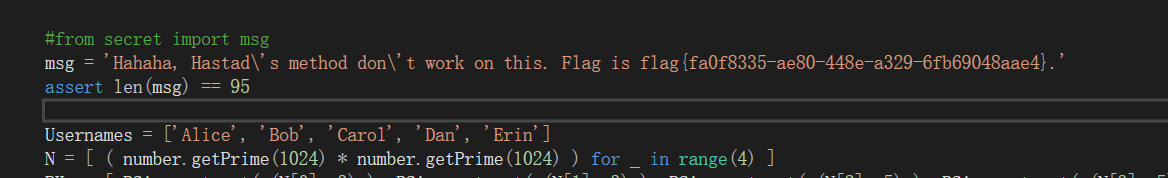
即得到flag:
flag{fa0f8335-ae80-448e-a329-6fb69048aae4}cr3-what-is-this-encryption
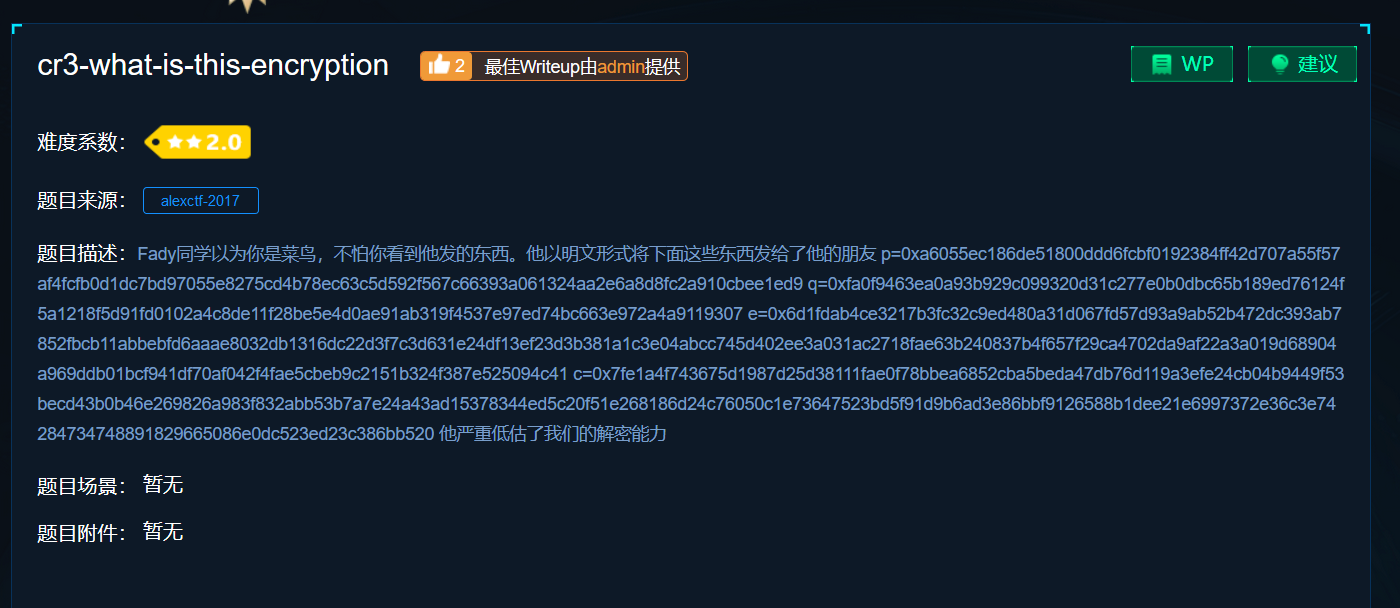
看到p、q、e、c就知道是rsa加密
脚本如下:
import libnum
from Crypto.Util.number import long_to_bytes
c = 0x7fe1a4f743675d1987d25d38111fae0f78bbea6852cba5beda47db76d119a3efe24cb04b9449f53becd43b0b46e269826a983f832abb53b7a7e24a43ad15378344ed5c20f51e268186d24c76050c1e73647523bd5f91d9b6ad3e86bbf9126588b1dee21e6997372e36c3e74284734748891829665086e0dc523ed23c386bb520
e = int("0x6d1fdab4ce3217b3fc32c9ed480a31d067fd57d93a9ab52b472dc393ab7852fbcb11abbebfd6aaae8032db1316dc22d3f7c3d631e24df13ef23d3b381a1c3e04abcc745d402ee3a031ac2718fae63b240837b4f657f29ca4702da9af22a3a019d68904a969ddb01bcf941df70af042f4fae5cbeb9c2151b324f387e525094c41",16)
q = int("0xa6055ec186de51800ddd6fcbf0192384ff42d707a55f57af4fcfb0d1dc7bd97055e8275cd4b78ec63c5d592f567c66393a061324aa2e6a8d8fc2a910cbee1ed9",16)
p = int("0xfa0f9463ea0a93b929c099320d31c277e0b0dbc65b189ed76124f5a1218f5d91fd0102a4c8de11f28be5e4d0ae91ab319f4537e97ed74bc663e972a4a9119307",16)
n = q*p
d = libnum.invmod(e, (p - 1) * (q - 1))
m = pow(c, d, n) # m 的十进制形式
string = long_to_bytes(m) # m明文
print(string) # 结果为 b‘ m ’ 的形式得到flag:
ALEXCTF{RS4_I5_E55ENT1AL_T0_D0_BY_H4ND}flag_in_your_hand1
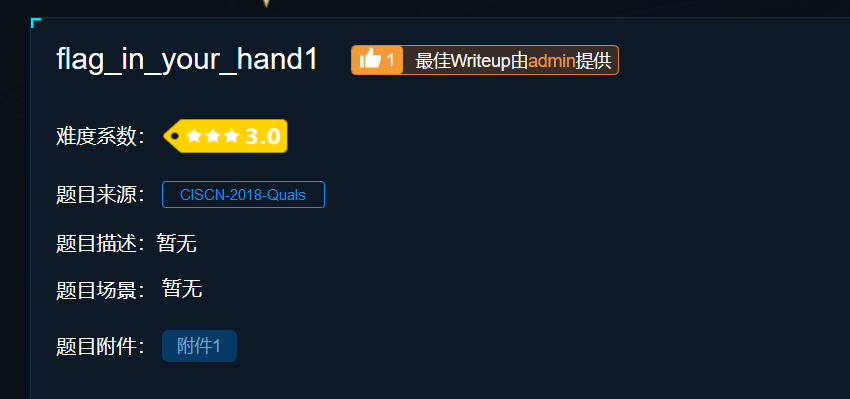
下载得到一个index文件和js文件,先打开index文件,找不到正确密码:
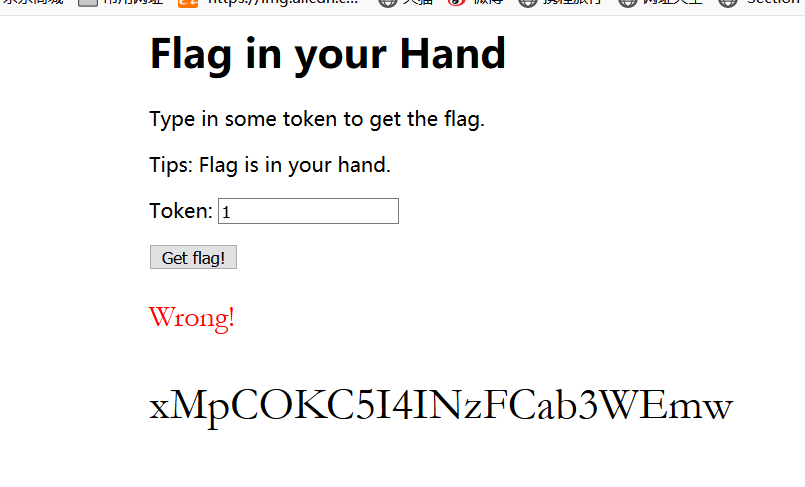
用vs打开js文件,找到a有着具体数据
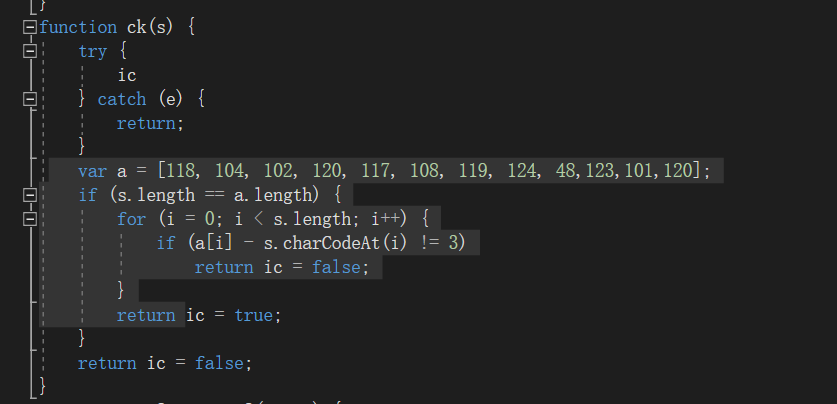
分析,写出脚本:
#include<iostream>
using namespace std;
int main()
{
int a[12] = { 118, 104, 102, 120, 117, 108, 119, 124, 48, 123, 101, 120 };
int b[12];
for (int i = 0; i < 12; i++)
{
b[i] = a[i] - 3;
cout << (char)b[i];
}
}得到:
security-xbu输入,密码正确,得到:
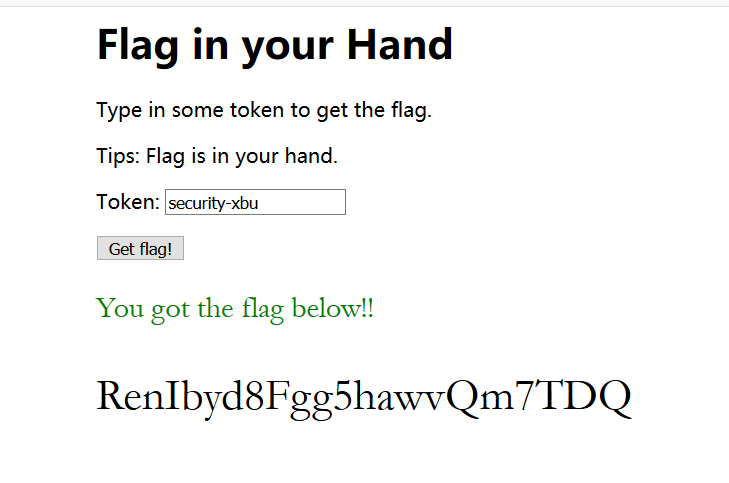
即flag:
RenIbyd8Fgg5hawvQm7TDQ工业协议分析2
下载后得到一个pcapng文件,应该是流量分析
用wireshark打开,发现很多UDP包
关键是很多包都差不多,感觉是在干扰,又只能一个一个去找
所以我看了下udp包的长度统计:
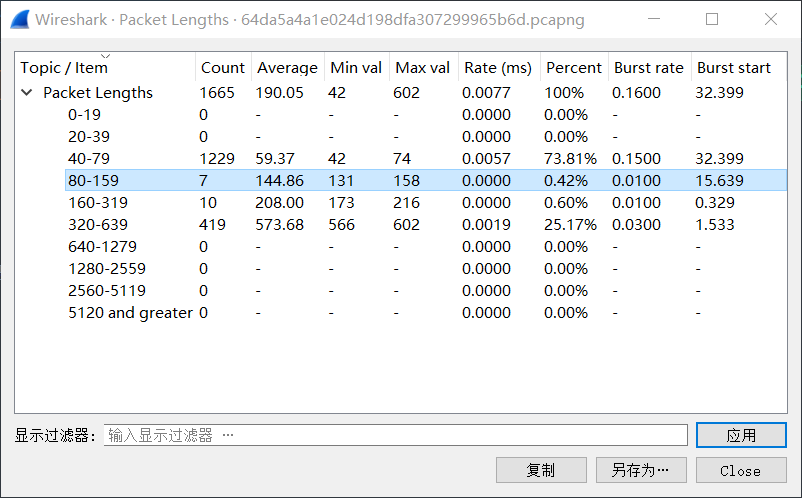
发现仅有17个包和其他不一样。
先找到试试,一个一个找,发现了一串hex数据:
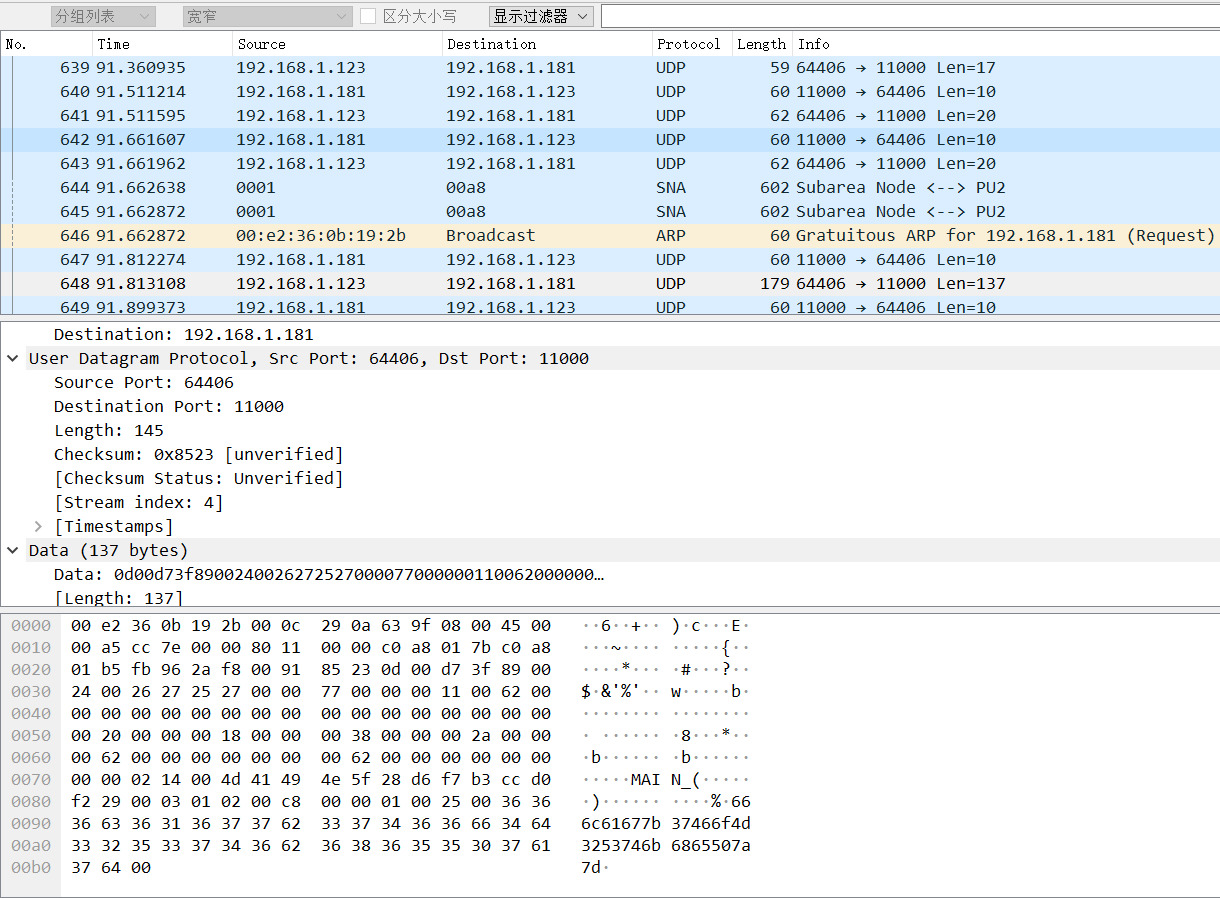
提取出来:
666c61677b37466f4d3253746b6865507a7dhex转ascii:

得到flag:
flag{7FoM2StkhePz}

